The Internet of Things (IoT) has revolutionized device connectivity. But it’s an aspect of IT which is still in its infancy. And mistakes are common.
The Internet of Things (IoT) has revolutionized device connectivity. But it’s an aspect of IT which is still in its infancy. And mistakes are common.
Eliminating these mistakes is an important factor in maximizing your productivity. After all, we live in a digital age. And it’s crucial that your IT systems are working to their full potential. Any drop off in productivity can harm the overall performance of your business. You need to retain an edge over your competitors, so mastering the IoT is crucial.
You may not be aware that you’re making mistakes with the IoT or you may not know how to rectify them. Either way you need a helping hand. And that’s why we’re going make sure you don’t make these common IoT mistakes.
Avoiding the Most Common IoT Mistakes
The IoT harnesses some complex technology, so it should come as no surprise that mistakes are common. However, these mistakes are relatively easy to fix:
- Not Defining Your IoT Needs: The IoT is an incredibly varied aspect of computing with many different uses. Understanding how you will implement it into your organization is vital. Therefore, you need to thoroughly scope out each project. Questions such as “How will it affect the workforce?”, “What are the costs?” and “Can it operate in our existing network?” need to be asked early on. Taking this approach will help you avoid implementation and operational issues further down the line.
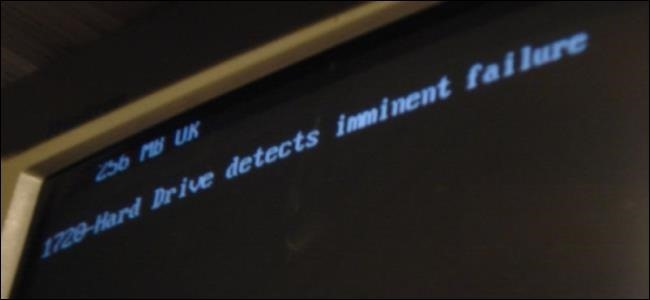
- Failing to Plan for Maintenance: IoT devices are like any other piece of machinery: they are prone to failure. And all it takes is for one device to fail to cause a massive drop in productivity. Scenarios such as this are why regular maintenance of your IoT needs to be built into your IT maintenance schedule.
- Ignoring Updates: The number of devices operating as part of the IoT is estimate to be just over 30 billion devices. That’s a lot of devices. And this has made them a target for hackers. But one of the simplest ways to protect your IoT devices is by installing any updates associated with them. Naturally, the number of devices means it can be difficult to monitor when updates are due. But, by running regular audits on your IoT devices, you can monitor for firmware and patches to maximize your security.
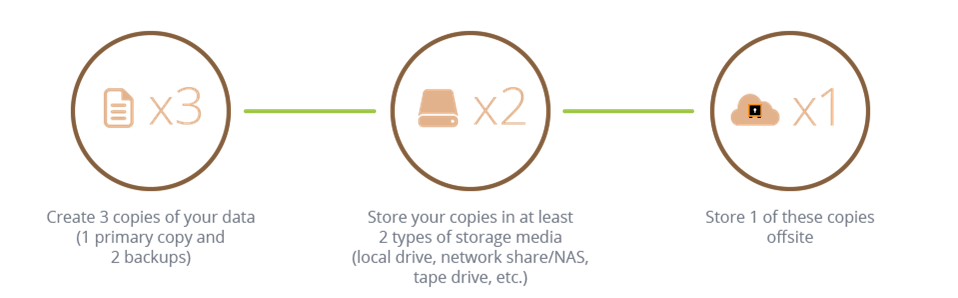
- Not Understanding the Importance of Data: IoT devices are fantastic for monitoring data, so it’s important that you take advantage of this. Vehicle tracking, for example, provides a wealth of information about the way in which your drivers are operating. And this data can be used to enhance their efficiency e.g. minimizing the risk of speeding offences and driving more economically. So you need to make sure that all IoT data is regularly analyzed.
By eliminating these common IoT mistakes you can make a significant difference to your organization’s productivity. IoT devices are only going to become more common in the workplace, so it’s important that you master this technology early on.
For more ways to secure and optimize your business technology, contact your local IT professionals.
Read More