by Ophtek, LLC | Jun 20, 2023 | IoT Attacks, malware, Ophtek, RapperBot, Security, strong passwords, Updates
Malware constantly evolves, and that’s why it’s a constant thorn in the side of PC users. The ever-changing RapperBot malware is a perfect example of this. If malware was boring and lacked innovation, it wouldn’t last very long or infect many computers. It would...

by Ophtek, LLC | Nov 23, 2021 | BotenaGo, Cyber Security, Internet Traffic, IoT Attacks, Ophtek, router, Software Security Patches
Routers and Internet of Things (IoT) devices are essential when it comes to modern business. But this has made them a target for the BotenaGo malware. Wireless technology is in place in almost every business in the world. The presence of routers allows PCs to connect...
by Ophtek, LLC | Apr 20, 2021 | Internet of things, IOT, IoT Attacks, Ophtek, Security
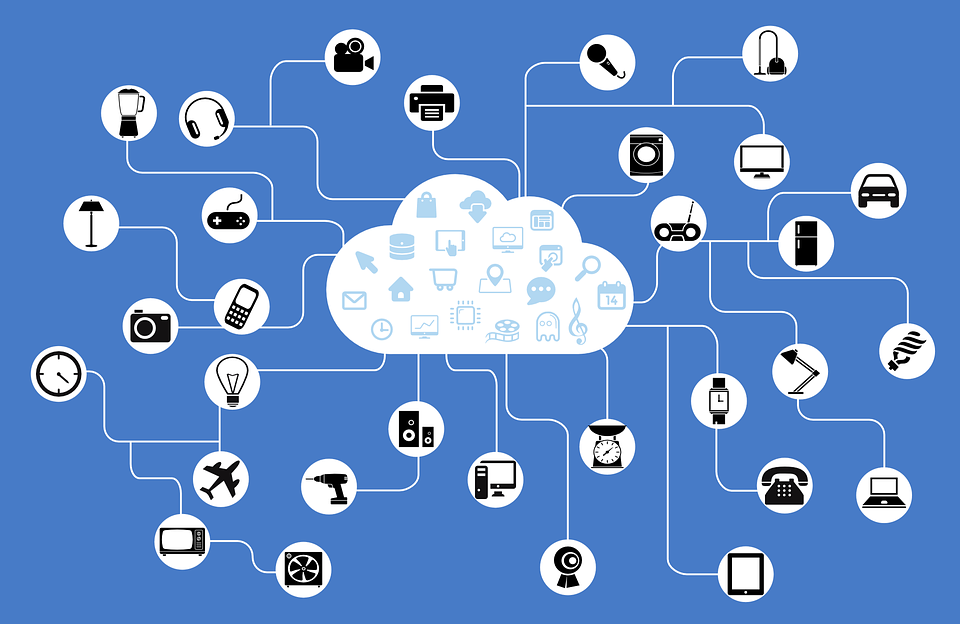
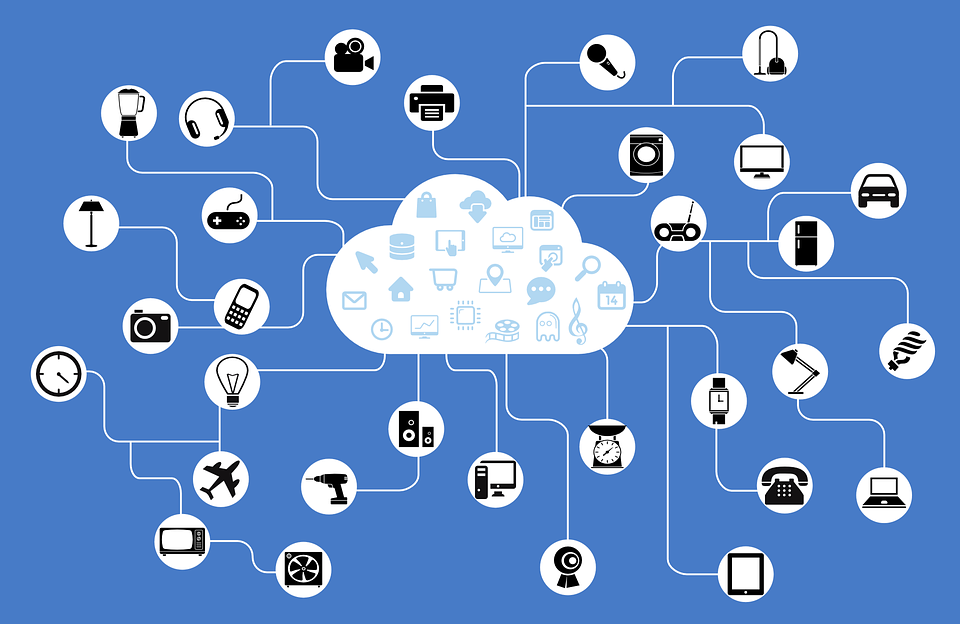
The Internet of Things (IoT) has redefined our concept of connectivity and what IT can achieve. But with these advances comes the need for unique security. Thanks to the IoT it is now possible for organizations to simplify their connectivity solutions. Traditionally,...

by Ophtek, LLC | Feb 4, 2020 | Internet of things, IOT, IoT Attacks, Ophtek, Uncategorized
The Internet of Things (IoT) has revolutionized device connectivity. But it’s an aspect of IT which is still in its infancy. And mistakes are common. Eliminating these mistakes is an important factor in maximizing your productivity. After all, we live in a digital...
by Ophtek, LLC | Jan 29, 2020 | IOT, IoT Attacks, IT Best Practices, Ophtek
The Internet of Things (IoT) is getting bigger and bigger. But this popularity is making it a target for hackers. Thankfully, Shodan is here to secure it. It’s difficult to imagine life without the IoT; the sheer range of possibilities it opens up is astonishing. But...
by Ophtek, LLC | Apr 16, 2019 | Internet of things, IOT, IoT Attacks, Ophtek, Security
The Internet of Things (IoT) has revolutionized the way we connect and interact with physical devices, but is this new technology as secure as it should be? Clearly, with around 26 billion associated devices estimated to be in use during 2019, the IoT needs to be...