Millions of workers are now self-isolating and that means working from home for many people. But how do you make sure that your PC at home is healthy?
The luxury of working from an office is that the equipment there is regularly maintained and fairly new. However, when you have to work from home you will soon realize that your own equipment isn’t in the same shape. We’re all guilty of being a little lazy when we get home and IT maintenance certainly isn’t at the top of most people’s lists. But a little effort goes a long way when it comes to maintaining a PC.
And, best of all, you don’t need to be a fully trained IT technician to carry out a home checkup. In fact, it’s quick and easy as we’re about to show you.
How to Maintain Your PC with a Home Checkup
Working from home on your own PC is convenient, but it also puts you and your organization at risk. Therefore, make sure you maximize your productivity and safety by carrying out the following:
- Install all Updates: We have a habit of ignoring PC updates at home as they get in the way of loading up Netflix. However, it’s important that complacency doesn’t creep into your IT activities at home. You need to make sure that all your software is up to date with the latest patches and firmware. Not only will this ensure that your software is secure, but it will enhance the functionality of your software. Most software will have an auto-update feature, so it’s crucial that this is activated.
- Check Your Router: The internet is vital when it comes to remote working. Without an internet connection you won’t be able to connect to your organization’s network. And this will leave you without any of the resources you need. So, it’s essential that your router is working and secure. A good connection is paramount, so you may need to adjust your router position to maximize the signal. And, to safeguard the security of your router, remove any default passwords and create something unique.
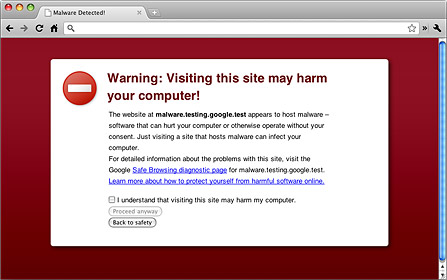
- Use Security Software: If you haven’t already got security software in place then this needs to be made a priority. It will protect your PC and, if you’re working remotely, strengthen the security of any connections to your business. There are a wide range of options when it comes to security software, so it can be daunting choosing one. It’s recommended that you stick to the industry leaders, so make a beeline to software developed by Kaspersky, McAfee and AVG. And you can rest assured that they provide plenty of free software.
Final Thoughts
The challenges of working from home are likely to be new for many employees. Thankfully, advances in technology mean that this is easier than ever. But you need to make sure that your PC at home is in excellent shape. It is, after all, your most valuable tool when it comes to working remotely. So, to guarantee a PC that is firing on all cylinders, you need to take note of the tips above.
For more ways to secure and optimize your business technology, contact your local IT professionals.
Read More