Google Fiber promises super fast broadband, but it remains out of reach for many people. However, it now looks as though it will shortly debut in San Jose. The days of conducting business over a 56k dial up modem seem like a lifetime ago and in the last decade the...
Blog

Malware Helps Protect Infected Routers
Malware is generally viewed as a nasty virus which causes nothing but chaos. However, a new piece of malware called Linux.Wifatch seems to improve security. Usually the preserve of security breaches and data privacy concerns, malware is mostly in the news for...
Microsoft Downloading Windows 10 To Your Machine Anyway
By now you will have seen the ‘Get Windows 10’ popup on your PC, but did you know that it’s being downloaded to your system even if you haven’t opted in? Microsoft has decided to start installing Window 10 on systems and this, of course, is eating into people’s...

More Pre-Loaded Lenovo Spyware
Several weeks ago, Lenovo was found to be preloading spyware onto their laptops; now it’s been discovered they’re loading spyware onto their Thinkpads. Yes, Lenovo has certainly disgruntled a whole new sector of customers. And what with the Thinkpad range being...

Predicting Failure: How Hard Drives Warn Us
Hard drives are valuable containers of data, so when they fail it can be costly. Therefore, it's essential you know how to monitor your hard drive's health. Now, you don't need to worry, as you don't need a PhD in computer health to analyze the health of a hard drive....

10 Security Best Practices for Businesses
It’s essential for businesses to protect their data assets from any potential security threat. Here are tips to help your business achieve this. The world of IT security, however, can be an intimidating landscape and many business owners struggle to put a plan of...
KeyRaider Malware Causes Havoc for Apple Devices
Users running Apple’s iOS software may have been exposed to a nasty piece of malware which threatens to steal user data and make unauthorized app purchases. This malicious software has been dubbed ‘KeyRaider’ and has been responsible for uploading sensitive user...

SmartPhone Malware Found on Popular Brands
It’s not just PCs that are at threat of malicious software (malware), smartphones are fast becoming the prime target for malware, but how has this happened? First of all, what exactly is malware? Essentially, it’s a nasty string of code or a program which enters...
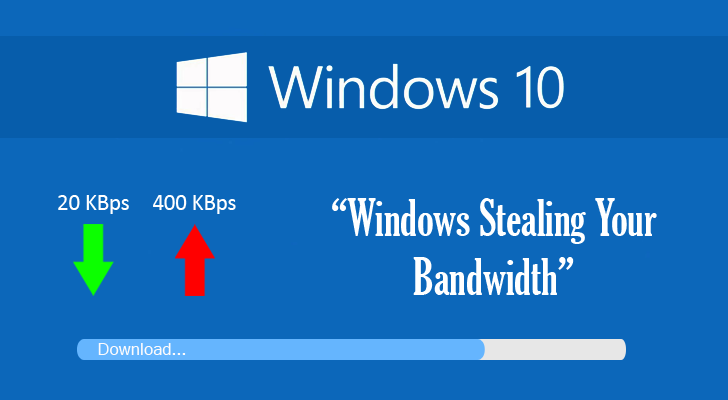
Windows 10 Blows Data Caps and Gives Some Consumers Huge Bills
Microsoft's Windows 10 claims to improve the PC experience, but the forced update is causing data caps to blow and creating financial chaos for its users. No one likes to receive a huge bill for their wireless costs, so many consumers are furious that this is...
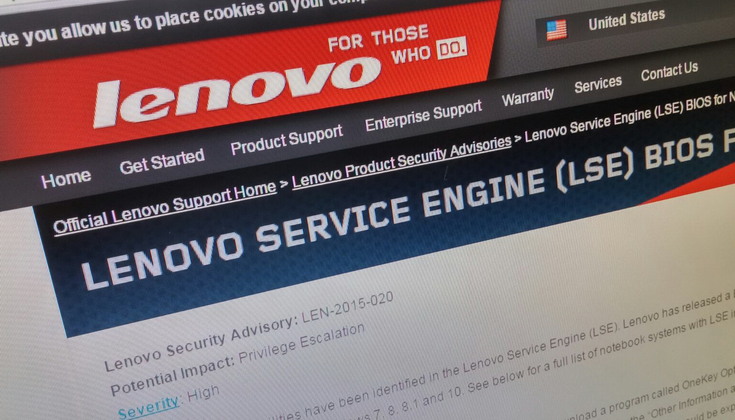
Lenovo Rootkit Fiasco
It’s irritating to find a fresh PC full of unnecessary preloaded software, but a Lenovo rootkit has been found sneaking software onto PCs after installation. Preloaded software such as this is called ‘bloatware’ as it uses up vital system resources, but provides...
