Advances in technology have created an environment where clocking in at the office is no longer required. But remote working is not without security risks.
Remote working is on the rise with many organizations offering this option to their employees. The benefits of remote working are numerous and apply to both employers and employees. But, away from the relative security of the office, remote working poses a number of security risks. Therefore, it’s crucial that your business finds a healthy balance. You need to develop a remote working environment which not only provides flexibility, but is also secure.
Achieving this combination is relatively easy. You just need to know how. And, thankfully, we’re going to show you how.
Keeping Remote Workers Safe
Remote workers are, to a certain degree, a law unto themselves. After all, working from a remote location means that immediate monitoring is next to impossible. So, you need to invest a certain level of trust. But we’re living in an age where cyber-attacks are reaching record highs. And this is why you need to help protect your employees in the following ways:
- Security Training: Your employees are your main defense against security attacks, so they need the correct training to remain safe. And this applies to remote workers more than any other employee. Regular training on security protocols and updates on contemporary threats need to be put in place.
- Use Two-Factor Authentication: One of the surest ways to secure your remote workers is by putting two-factor authentication in place. This is a security procedure by which users have to provide additional information alongside a username and password. This can take the form of a PIN number sent to a mobile device or a secret question. It only takes seconds to pass two-factor authentication, but the enhanced security it provides is priceless.
- Monitor Devices Closely: It’s important to keep a regular eye on any company issued devices that are used remotely. For one thing, you need to make sure that your employees are working as they should be. But, when it comes to security, you should make sure you are analyzing their usage e.g. visiting malicious websites and connecting external devices such as USB drives.
- Implement a VPN: A virtual private network (VPN) is essential for remote workers. It’s difficult to guarantee that remote connections are fully secure, but a VPN solves this problem. Using multiple layers of encryption, a VPN protects any data being transmitted or received by remote workers. Therefore, data such as financial records and customer details will be secured from any external forces.
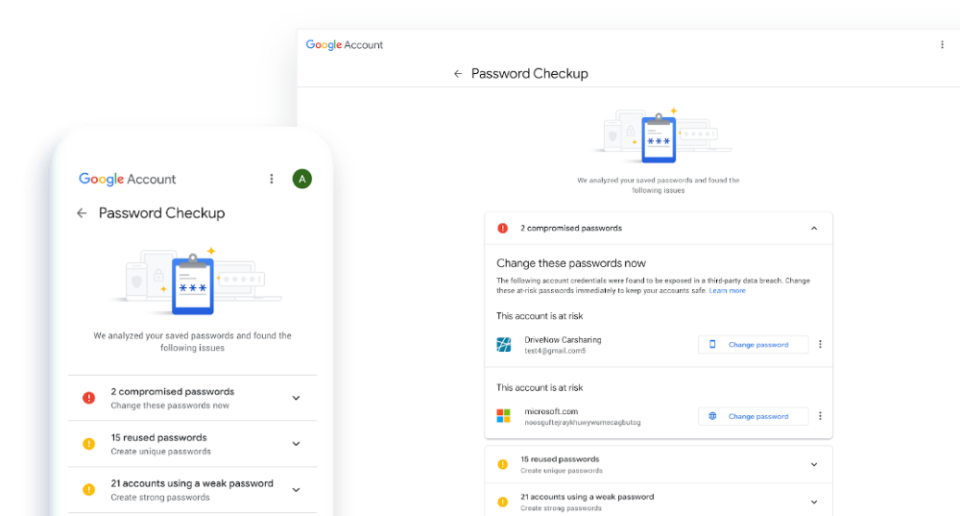
- Use Strong Passwords: This may sound simple, but a weak password is easier to crack than a complex one. However, this advice is ignored more often than you would think. So, you need to remind your employees of the importance of password security. And you need to prompt them to regularly change their passwords. Thankfully, creating strong and unique passwords is easy once you learn the basics.
For more ways to secure and optimize your business technology, contact your local IT professionals.
Read More