There’s only one thing worse than malware and that’s malware which is difficult to detect. And PowerPepper is incredibly difficult to detect.
Discretion is one of the most crucial aspects of any form of hacking. A well-executed hack should remain invisible to the victim for as long as possible. Such a scenario allows a hacker to cause maximum damage and also gives them time to cover their tracks. Thankfully, good security practices should either eliminate this risk from happening or, where anti-malware apps are in place, provide an early warning. But hackers are well aware of these defenses and are constantly trying to outwit them.
The emergence of the PowerPepper malware demonstrates that hackers have (temporarily) succeeded in hiding their activities better than ever before.
What is PowerPepper?
PowerPepper, discovered and named by Kaspersky, is a new strain of malware which is believed to have been designed by hacking group DeathStalker. Active since 2012, DeathStalker has made a name for themselves by developing numerous strains of innovative malware. Complex delivery chains are their trademark, but what really stands out is their dedication to evading detection. And PowerPepper is the latest development in DeathStalker’s abilities.
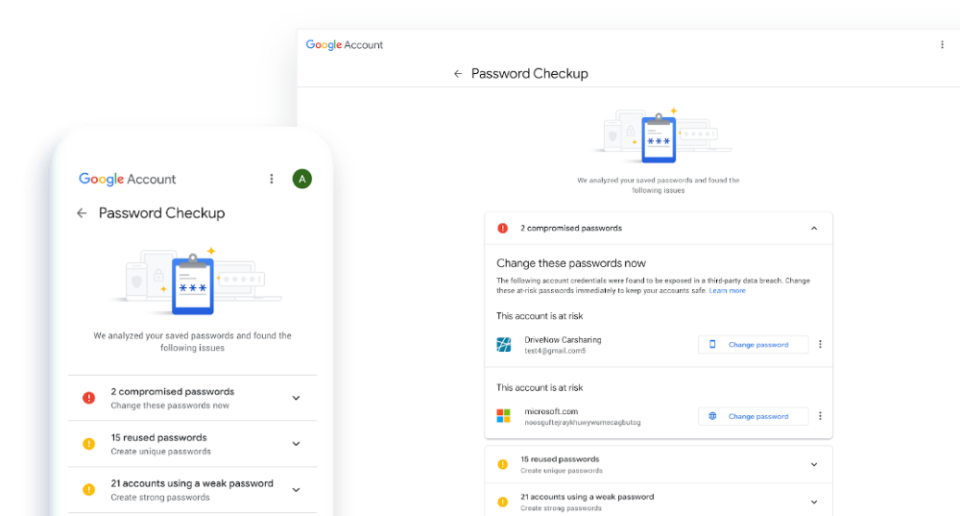
First discovered in May 2020, PowerPepper allows hackers to carry out shell commands from a remote location. But what is a shell command? It’s not something that the average PC user will ever carry out, but a shell command allows you to control your computer by using commands entered with a keyboard through special apps such as Terminal. Naturally, this is a highly valuable app to exploit and DeathStalker have made sure that PowerPepper is not detected. It does this by filtering the clients MAC address, tailoring its processes to deceive anti-malware tools and evaluating mouse movements.
For PowerPepper to take hold, of course, it needs to get on to a victim’s PC. And it does this through a variety of spear phishing campaigns. These attacks utilize both malicious links and email attachments in a number of ways aimed at reducing detection e.g. hiding malicious code in embedded shapes in Word documents and using compiled HTML files to obscure malicious files.
How Do You Protect Your PCs?
PowerPepper has already gone through a number of changes since it was first discovered, so keeping on top of it is difficult for even the most knowledgeable PC user. However, there are plenty of preventative measures you can take:
- Install all Updates: One of the surest methods to protect your PC systems is by ensuring all their software and hardware is up to date. This is easily achievable by installing all the relevant updates your system needs. The last thing that you want to present malware with is a back door entry point, so eliminate this by installing all updates.
- Restrict Access to Shell Terminals: There’s little need for your PC users to have access to shell terminals, so it makes sense to restrict this access. By removing this privilege you are also removing the risk of hackers taking control of such a powerful app.
- Be Wary of Attachments: Malware such as PowerPepper makes its way through the digital landscape thanks to a lack of vigilance on the part of PC users. This is most often demonstrated by opening malicious email attachments. Therefore, it’s crucial to evaluate all email attachments before opening them.
For more ways to secure and optimize your business technology, contact your local IT professionals.
Read More