Several weeks ago, Lenovo was found to be preloading spyware onto their laptops; now it’s been discovered they’re loading spyware onto their Thinkpads.
Yes, Lenovo has certainly disgruntled a whole new sector of customers. And what with the Thinkpad range being marketed as a business laptop it’s particularly worrying for business customers.
After all, which business wants to get caught up in any type of security threat which could potentially distribute their customers details to third party sources?
Let’s take a quick look at exactly what’s happening.
The Spyware Scandal
The Thinkpad range was purchase by Lenovo from IBM and these refurbished models are being packaged with a piece of software called ‘Lenovo Customer Feedback Program 64’ which is causing the latest controversy.
But what exactly does this spyware do?
Well, it’s there to send customer feedback back to Lenovo’s servers to help improve their products and service. There’s not anything particularly nefarious about that. However, it’s also been discovered that this piece of software contains the following files:
- TVT.CustomerFeedback.OmnitureSiteCatalyst.dll
- TVT.CustomerFeedback.InnovApps.dll
- TVT.CustomerFeedback.Agent.exe.config
It’s the first file which is interesting as it relates to Omniture who are an online marketing and web analytics company. What they do is monitor people’s behaviour online to help build a snapshot of how internet traffic is moving across the web.
Now, although Lenovo do disclose in their EULA (End User Licence Agreement) that software will be transmitting customer feedback to the Lenovo servers it is buried away amongst a lot of text. Additionally, there is no mention that internet usage will be monitored and passed on to Omniture for what is surely financial profit.
Just imagine the security risks this could have with your business if hackers are able to find a loophole in this spyware and can piggyback onto your internet connection? It could spell serious security issues for the security of yours and your customers’ data.
Removing the Spyware
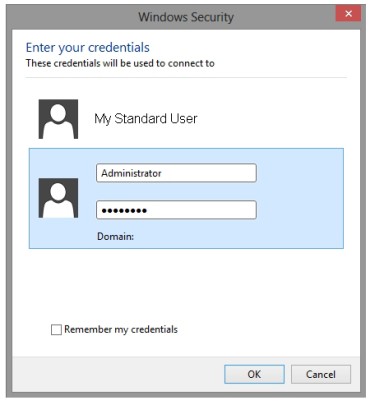
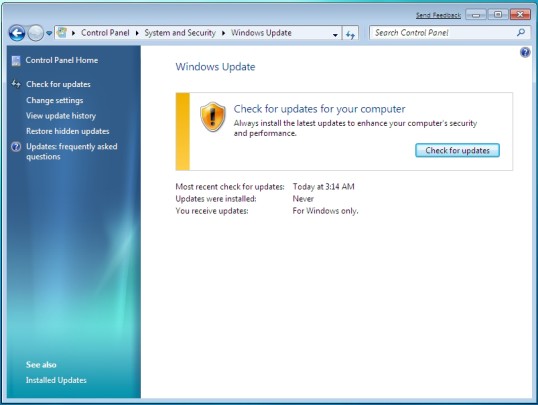
Thankfully, it’s not a mammoth task when it comes to removing the spyware, so just follow these steps:
- Download ‘Task Scheduler View’ which is a useful piece of software which displays all the tasks running in Windows
- Within Task Scheduler View you will want to disable anything which is related to Lenovo customer feedback and/or Omniture
- It’s also recommended to rename the folder “C:\Program Files (x86)\Lenovo” e.g. “:\Program Files (x86)\Lenovo-test” to help prevent any other dubious files being activated or installed
This should that your Thinkpad and your confidential data remain secure and are not at risk of being exploited.
When Will Lenovo Stop?
This is the third security scandal to hit Lenovo this year after the Superfish and BIOS modifying controversies, so consumers are understandably losing their patience with Lenovo.
Although Lenovo claims on their website that “Lenovo takes customer privacy very seriously and the only purpose for collecting this data is to improve Lenovo software applications” it remains to be seen when they will follow through on this pledge.
For more ways to secure and optimize your business technology, contact your local IT professionals.
Read More