Java is required by many applications and websites to work properly. It can also be exploited by criminals. Here’s why you should keep your java up to date.
Many business users need it to run custom or legacy applications. Java is not just for gamers. It is used by countless business applications.
Java Security Risks
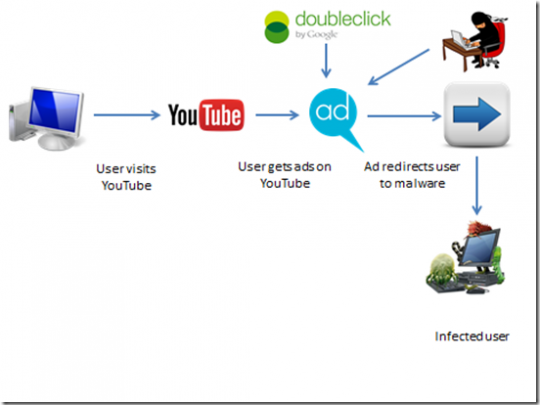
As recently as January, hackers were able to exploit a security hole in Java to serve up malware to hundreds of thousands of systems per hour.
It is because of these security holes and many others that Java must be updated frequently.
Java often uses your web browser to access websites, and your web browser is the most vulnerable attack surface for hackers. Therefore, not updating Java religiously is playing with fire.
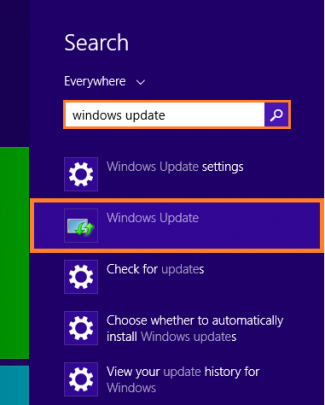
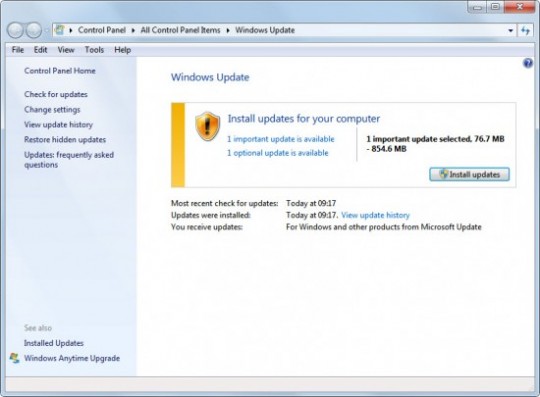
How to Update Java
First, find out if you have the latest version here.
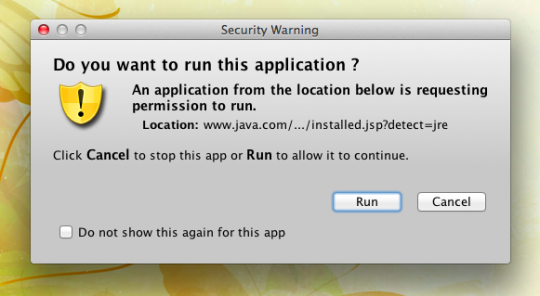
Click the red Verify Java version box to allow Oracle’s website to find out if you have the latest version installed. If you are given a prompt stating Allow the Java plugin for your browser, click to allow it. Next, another prompt will likely appear as shown below:
Click Run to allow the application to run. If you have reached this stage, you have Java, though not necessarily the latest edition. If you have the latest Java, you should get a window telling you Congratulations with an accompanying green check. If you don’t have the latest Java, you should see a screen that looks like this:
Click Click Download Java Now to get the latest version of Java.
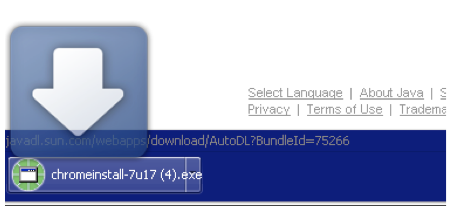
Click the red Agree and Start Free Download to get the newest Java for your system. The progress of the download should appear at the bottom of your browser. It will finish when no time appears next to the download.
Click the .exe file to kick off the installation. You should promptly close your browser to avoid any roadblocks or conflicts.
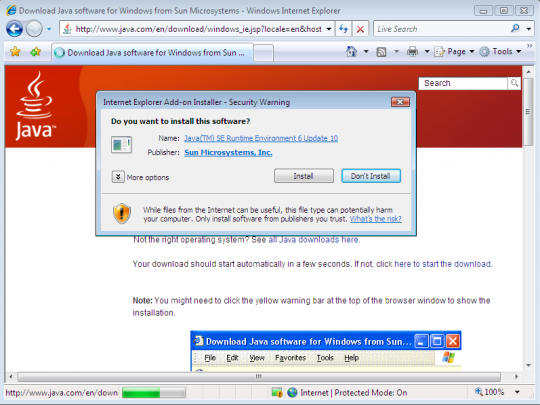
When the security warning appears, click Install to permit the latest Java to be installed.
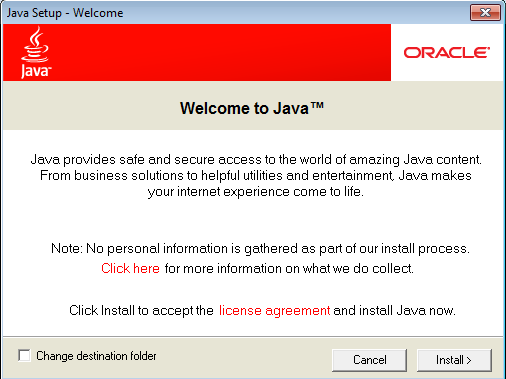
On the Welcome to Java screen, click Install again to allow the installation to proceed. At some point during the installation, you will see the following window:
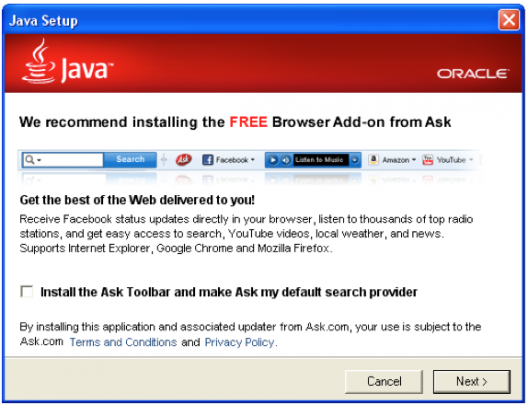
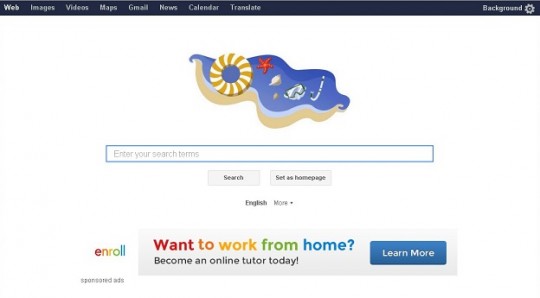
At all costs, do NOT check the Install the Ask Toolbar and make Ask my default search provider option. The Ask Toolbar is completely unnecessary and makes your computer more vulnerable to infections. Click Next to allow the final steps of the installation.
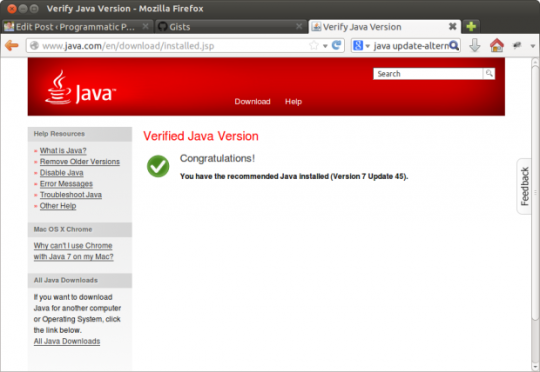
After the green progress bar reaches the end, you will be directed to Oracle’s website where you will again see the following:
As before, click the red Verify Java version button. Once again you should click Allow to enable the website to see what Java version you are running. Also, click Run in the following window to enable the test.
If you have the latest Java, you will see the following window:
If the website still tells you your Java is outdated, go through the earlier steps starting with Download Java. If you have already downloaded and installed the latest Java and you get the outdated message, simply closing and reopening your browser will often correct the problem. Go back to Oracle’s website to verify your Java version.
For more about Java or other security issues affecting your home or office computers, consult with your local IT professional.
Read More