Malware is a thorn which we find in our sides on a regular basis. But what happens when this thorn becomes even harder to tackle? The answer is Trickbot.
First released in 2016, Trickbot has made its name by using a variety of attack methods. The malware has been shown to steal Bitcoin, target banks and harvest login credentials. Naturally, this makes it a very dangerous piece of malware. But as with a virus that attacks humans, this malware is constantly changing its DNA. New features have regularly been added to Trickbot which not only makes it harder to detect, but also makes it more dangerous.
Trickbot has the potential to cause significant damage to your IT setup, so it’s important to know what you’re up against.
The Lowdown on Trickbot
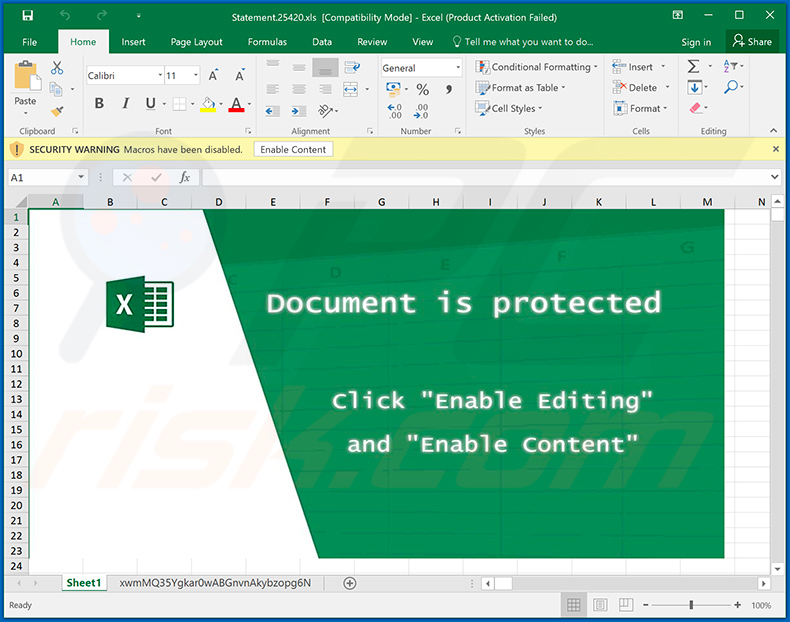
The most common infection method used by Trickbot is through the use of malicious spam campaigns. Emails that pretend to be from financial institutions are used to distribute infected attachments and URLs that the victims are urged to action. And, once the payload has been activated, it’s unlikely that the victim will be aware. Trickbot will communicate with a remote command and control centre almost silently and, at the same time, infect other PCs on the same network.
Trickbot’s Latest Trick
As we mentioned earlier, the hackers behind Trickbot thrive upon their ability to evolve the malware. And their latest upgrade to Trickbot is both innovative and deceptive. This is most keenly demonstrated by its ‘anti-virtual machine’ strategy. One of the safest ways for security professionals to analyze malware is within a virtual machine environment. Therefore, in order to hide its operations, Trickbot will stop working when it detects a virtual machine.
And, believe it or not, one of the simplest ways to do this is to analyze the PCs current screen resolution. Any screen resolution that is set to 1024×768 and below will cause Trickbot to terminate its operations. This means that security researchers using a virtual machine to will draw a blank. This is a very clever technique and is one that allows Trickbot to reactivate once the PC is restarted into a higher resolution.
How Do You Stop Trickbot?
Anti-malware software such as Malwarebytes is capable of detecting and removing most strains of Trickbot, but there will always be a slight delay when it comes to new strains. And, of course, you should never rely on removing infections as the best strategy for defense. Instead you should make every effort to prevent infection in the first place. This can be achieved in the following ways:
- Evaluate All Incoming Emails: It’s essential that your staff is aware of the dangers of phishing emails. Thankfully, the tell-tale signs are easy to detect and, with this knowledge to hand, it should become much harder to fall victim to Trickbot.
- Patch Any Vulnerabilities: Trickbot hasn’t, as of yet, been shown to exploit software vulnerabilities. But given its innovative and evolving approach it’s likely this will become part of its strategy in the future. And that’s why it’s vital all patches are installed and implemented as soon as they are available.
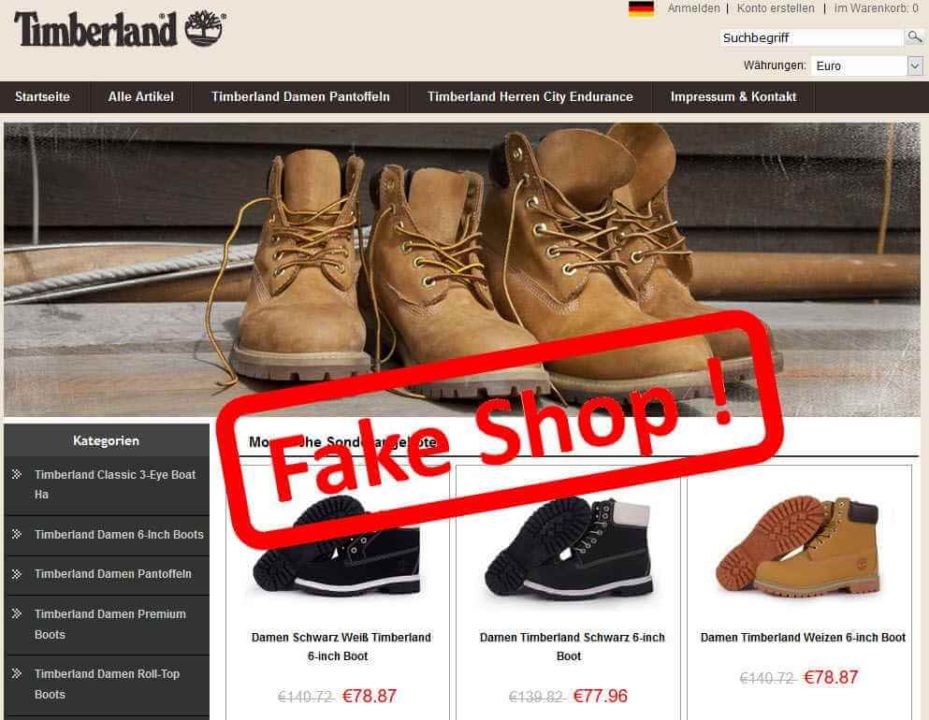
- Avoid Malicious Websites: Given their deceptive nature, it’s easier said than done to avoid malicious websites. However, it’s crucial that you have the ability to identify malicious websites. This will severely limit the chances of downloading malware such as Trickbot.
For more ways to secure and optimize your business technology, contact your local IT professionals.
Read More