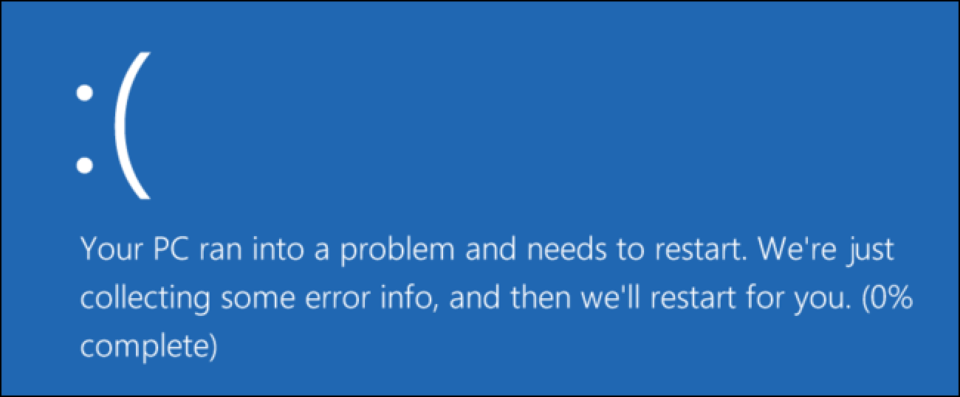
It’s highly frustrating when a PC crashes during the startup process. However, there is always a reason behind every crash and this means it can be fixed.
All we want at the beginning of each day is an easy start, so a PC which boots up quickly with no problems is a big help in this respect. But a PC which struggles to startup correctly can seriously set you back. Not only does it leave your frustration levels skyrocketing, but it puts the brakes on your productivity. A PC, of course, is a complex device and occasional problems should be expected. Thankfully, PCs operate on logic, so rectifying a startup problem is simply a case of identifying where this logic has failed.
The Most Common Startup Problems
To help you overcome your startup woes, we’re going to examine the most common reasons why your PC is crashing at startup:
- No Bootable Medium: If you are confronted by a black screen containing a message along the lines of “No Bootable Medium Found” then you are going to have a problem. What it means is that your PC is unable to boot from the hard drive it is programmed to. It could be that the order in which your PC is designed to boot from has become corrupted e.g. your PC heads straight to your D: drive rather than the C: drive. This can easily be checked and amended in your PC’s BIOS setup – this can be accessed by pressing a designated F key as your PC powers up.
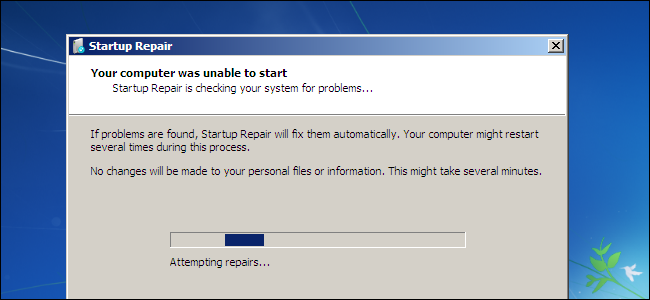
- Missing Files: If Windows is missing just one file then it can cause major problems for your PC. So, if a file has been mistakenly been deleted or moved from its correct location, it’s likely that problems will be around the corner. And this can include issues with your startup process. The simplest way to deal with these incidents is by repairing your Windows installation. In Windows 10 this can be initiated by running the ‘Reset This PC’ tool. However, it’s likely you will need to boot Windows in Safe Mode to access this if you are already having startup issues.
- Malware: There are many types of malware which can cause your PC to crash during startup, so it’s important to consider this. Naturally, the only way to remove this problem is by removing the malware. But how can you do this when you can’t get into Windows? Well, again, this is where Safe Mode comes in. Although Safe Mode only gives you limited access to normal Windows operations, it does give you access to antivirus software. Therefore, you have the chance to eliminate any malware and restore your startup.
- Hard Drive Data Cable: Your PC needs to be able to access your hard drive in order to boot up Windows, but problems can quickly occur if this access is restricted. And a failed hard drive data cable is one of the surest ways for this to happen. If your PC is regularly freezing at startup or entering reboot loops then it makes sense to try replacing this cable. If this solves the problem then you are good to go and, if it doesn’t, then you can investigate further solutions.
For more ways to secure and optimize your business technology, contact your local IT professionals.
Read More