by Ophtek, LLC | Aug 21, 2018 | Internet of things, IOT, IT Best Practices, IT Plan
There’s a good chance that the benefits of the Internet of Things (IoT) could make a huge difference to your organization, but how do you get started? With around 30 billion IoT connected devices due to be in use by 2020, the IoT is clearly here to stay and the...
by Ophtek, LLC | Jun 26, 2018 | Internet of things, IOT, Productivity
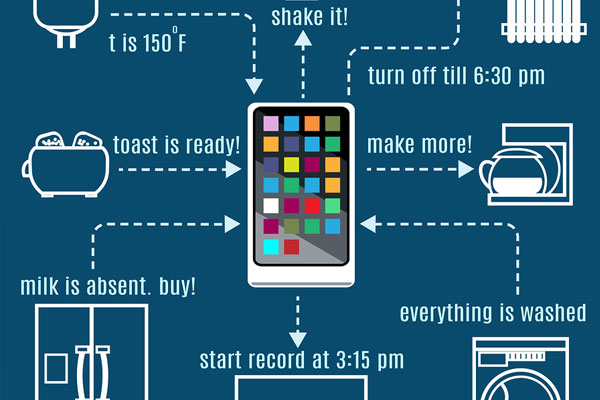
The Internet of Things (IoT) has revolutionized the way we do business thanks to the accessibility on offer, but are you getting the best out of it? More and more organizations are using IoT devices to help improve their business operations and it’s estimated that...

by Ophtek, LLC | Mar 8, 2018 | Cyber Attack, Hacking, Internet of things, IOT, malware, Password Security, Security, Security Threats
The Internet of Things (IoT) has a new security threat and this time it uses peer-to-peer communication to spread, infect and compromise devices. In January 2018, security researchers working for Bit-defender discovered a new botnet which, although not related, has...

by Ophtek, LLC | Mar 6, 2018 | Company Updates, Cyber Attack, Hacking, Internet of things, IOT, Security, Security Threats
The Internet of Things (IoT) has many security concerns, but perhaps one of the most pressing worries is that IoT devices can be easily hacked for just a few dollars. A group of elite hackers have recently demonstrated the ease with which a hardware hack can be...
by Ophtek, LLC | Feb 27, 2018 | Hacking, Internet of things, IOT, Network, Security, Security Threats
The Internet of Things (IoT) is amazing, but it’s not perfect and, in particular, there are plenty of security vulnerabilities that you need to know about. You can barely move without bumping into an IoT device now and, whilst this allows you to be more productive, it...

by Ophtek, LLC | Feb 20, 2018 | Cyber Attack, Hacking, Internet of things, IOT, IoT Attacks, malware, Phishing, Ransomware, Security, Security Threats
If you want to keep the IoT (Internet of Things) secure in 2018 then you’re going to have your work cut out due to the number of threats on the horizon. Significant progress has been made in the last couple of years when it comes to understanding the security concerns...