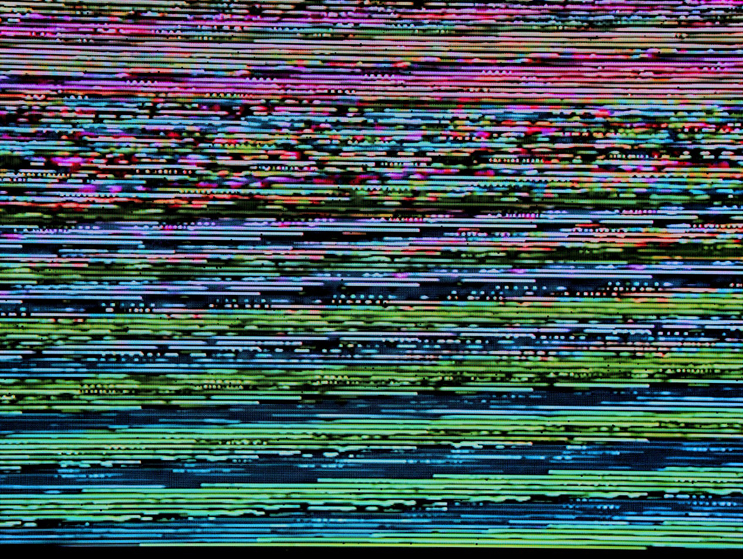
The world of illegal downloads is a dangerous place to travel to and the emergence of the CopperStealer malware demonstrates why.
Ever since the dawn of the world wide web, there have been illegal downloads. And pretty much anything that runs on a PC can be downloaded illegally. The new Kings of Leon album, the latest Marvel movie or even the most up-to-date version of Microsoft Office can be found online for zero dollars and zero cents. However, the fact that these downloads are illegal means that, aside from the fact that you’re committing a felony, you could download more than you bargained for.
CopperStealer is the perfect example of this dangerous activity, so we’re going to show you exactly what can happen.
What is CopperStealer?
The CopperStealer malware is believed to have been active in the wild since 2019, but its malicious activity has only just been detected. CopperStealer relies on illegal downloads to infect workstations and does this by either masquerading itself as, for example, a Windows 10 install file or by bundling itself with a genuine piece of software. Either way, when the person downloading the file tries to install their illegal software, they will inadvertently install CopperStealer on their system. This allows the malware easy access to PCs and does it with the help of the unwitting victim.
Once CopperStealer has taken hold on a PC it begins working quietly in the background as it harvests user information. In particular, it’s exceptionally hungry for login credentials; details for major platforms such as Amazon, Google, PayPal and Twitter have all been targeted by CopperStealer. These are all websites that are used by organizations to store huge amounts of personal data, so the threat that CopperStealer represents is serious. As well as this major threat, CopperStealer also finds time to download additional malware in order to compromise infected systems even further.

How To Protect Yourself from CopperStealer
There is one simple move you can make to defend yourself against CopperStealer: don’t get involved with illegal downloads. Not only is there the threat of unwanted malware being bundled with them, but you risk installing unpatched software without the safety net of available support. Thankfully, CopperStealer is far from sophisticated, certainly compared to other contemporary malware, and can easily be removed with anti-malware software such as AVG and Kaspersky products. Naturally, you will want to make sure that your anti-malware application is fully up to date to protect against all the latest threats.
Final Thoughts
The temptation of illegal downloads, especially when we are living in a time of economic turbulence, is strong, but it pays to resist it. If, for example, your PayPal credentials are stolen then you and your customers could face some significant financial hardship. Therefore, it’s crucial that you always pay for your software. This will, as discussed, ensure you receive regular updates and patches as well as providing you with peace of mind that your software is clean.
For more ways to secure and optimize your business technology, contact your local IT professionals.
Read More