Having your organization’s network breached is a major cyber disaster, so identifying a breach quickly is crucial. But how do you know you’ve been hacked?
Protecting your organizations networks and data is essential, but with the huge number of hacks taking place it’s not easy. And if a breach occurs this can cause multiple problems for your business such as data theft, ransomware demands and damaged networks. When it comes to these attacks then there’s one factor which is essential: speed. The sooner you realize you have been hacked, the sooner you can set about cleansing your system. Hackers may be evolving their methods to become even stealthier, but there are still certain tell-tale signs that you’ve been hacked.
You may not be aware of these indicators, so we’re going to share five signs that you’ve been hacked.
What Are the Signs of Being Hacked?
The most obvious indicators of your PC being hacked are the following:
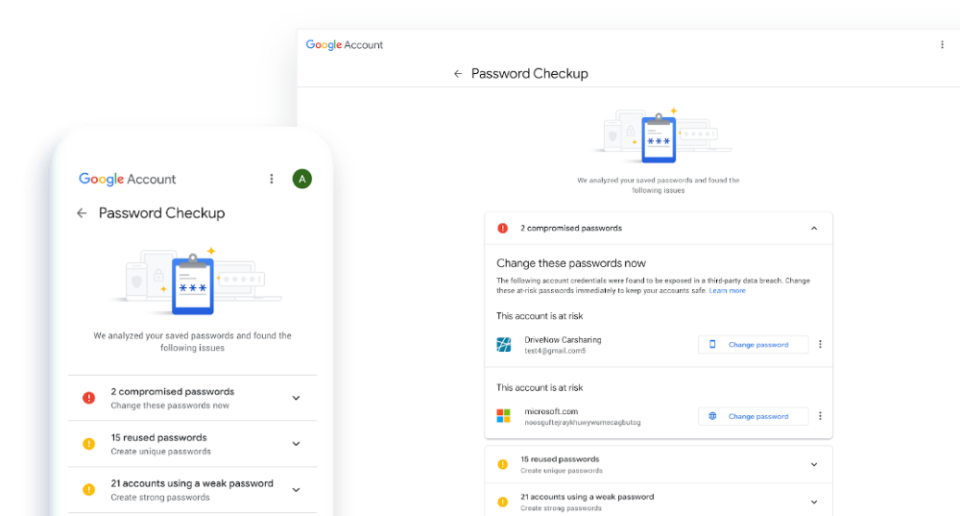
- Password Not Working: One of the simplest signs of falling victim to a hack is when your password isn’t working. Sure, there’s a chance that you’ve mistyped it or simply forgotten it, but alarm bells should start ringing if you’re convinced you’ve got it right. And, if you have activated two-factor authentication and this is also not working, it’s likely your login credentials have been breached.
- Your Browser Keeps Redirecting: If you discover that your internet browser is behaving strangely then this is a sign you have been hacked. Your browser should, for example, open up with either your company home page or Google, but a hacked browser is likely to take you straight to a malicious website. Such a website will prompt you to download files in an attempt to infect your PC with malware. If this happens then you need to close the browser as soon as possible and advise an IT professional.
- Your Anti-malware is Disabled: It’s unlikely that you will ever need to disable your anti-malware software, so any indication of this being disabled could signal a hack. After all, hackers want to make their life as easy as possible. Therefore, if they take control of your PC, the simplest way to download malware undetected is to disable your defenses. Make a point of regularly checking the status of your anti-malware software to stay safe.
- A Mouse Cursor With a Mind of Its Own: Your mouse cursor should, if you’re not moving the mouse, stay still. You may occasionally get a small amount of movement from hardware issues, but any significant movement indicates a hack. If your PCs defenses have been breached then hackers can easily take control of your PC. And this can be evident from unauthorized activity taking place on the screen. So, if you find that applications are being launched without your permission, power off your PC and immediately get it investigated.
- Your PC is Slowing Down: A PC can slow down when it’s processing multiple tasks at once, but one which is slowing down for no particular reason is one to be suspicious of. It could be, for example, that your PC has fallen victim to a botnet and your PCs processing power is being harnessed for attacks elsewhere. If, after restarting your PC, it continues to lag then it’s critical that you take the necessary measures to isolate that PC before looking deeper.
For more ways to secure and optimize your business technology, contact your local IT professionals.
Read More