Many people have resisted migrating from Windows 7 and 8.1 to Windows 10, but Microsoft has now announced that new processors will only run on Windows 10.
You might have noticed, last summer, that windows were popping up on your PC encouraging you to switch to Microsoft’s latest operating system (OS) – Windows 10. However, a high percentage of users avoided hitting the ‘INSTALL’ button.
You see, Windows 8 was somewhat of a disaster for Microsoft, both technically and aesthetically. As a result, consumers were reticent to take up Microsoft’s offer of a free upgrade as they had no idea what would be waiting for them.
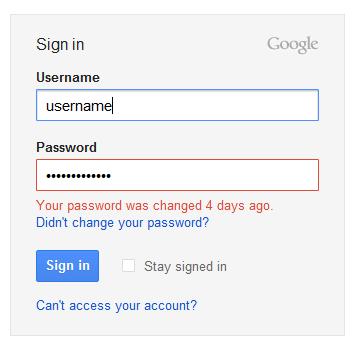
These fears were further compounded when story after story emerged of issues with Windows 10 e.g. security flaws and Microsoft actively forcing installs onto users’ systems. As I’m sure you’ll agree, though, progress is always necessary, so you were probably going to give in at some point.
Microsoft has decided to try and force your hand a little sooner with their announcement that new processors will only be compatible with Windows 10, so let’s take a look at what this means for you and your business.
What Exactly Has Microsoft Announced?
Microsoft is keen for the latest processors being designed to use the most up to date Windows OS. This means that new processors released by AMD, Intel and Qualcomm will only work on PCs running Windows 10. If you’re running an old OS, they simply won’t work. And when Windows 11 comes around, the exact same procedure will be put in place.
Why is Microsoft Making This Policy Change?

Upgrading previous versions of Windows always had a financial pinch for consumers, but Windows 10 is completely free. This is all part of Microsoft’s plan to market Windows 10 as a service rather than a costly product.
Microsoft wants everyone to adopt it, so ensuring that Windows 10 is essential for new processors means there will be no choice but to upgrade.
It’s also a move which will keep hardware developers for Microsoft happy as they will no longer have to outlay huge amounts of cash on making their processors backwards compatible.
Does This Mean You Have to Upgrade Immediately?

You might be concerned that Windows is forcing you to not only upgrade to Windows 10, but also to upgrade to one of the new processors. However, this couldn’t be further from the truth.
Windows 7 and 8.1 will still receive essential security and application updates for several years, so, as long as your hardware stays the same, your OS will remain supported.
However, remaining on an ‘antiquated’ OS is not the best way for your business to stay competitive and work to its full potential. That’s why it seems as though it’s only going to get harder and harder to resist the upgrade to Windows 10.
For more ways to secure and optimize your business technology, contact your local IT professionals.
Read More