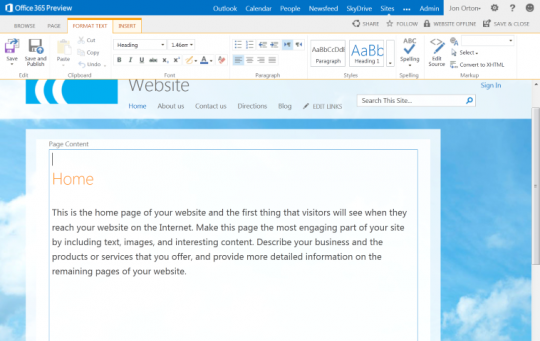
Noam Liran, the chief software architect at Adallom, recently detected a flaw in Microsoft Office 365 which can easily expose account credentials through Word Documents that are hosted on a webserver which is currently invisible to existing anti-virus software.
What Specifically Is The Problem?
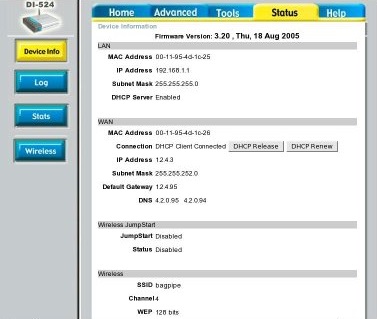
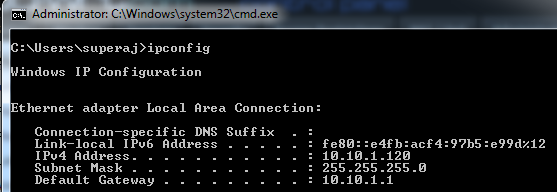
When a user downloads a document from a SharePoint server, the user is required to log in their account first – after which the server verifies the login credentials and then issues an authentication token. Liran discovered that he can use his own server to copy the responses which are sent from the sharepoint.com domain server. At that point he can generate and fake the token. An attacker doing this can inject his code to connect to an untrusted web server to capture the user’s private Office 365 authentication token. This allows the attacked to go to the user’s organization’s SharePoint site to access anything they want without the user knowing. According to Liran this is a perfect cyber crime in which the organization does not know they have been hit.
Microsoft has been working on this vulnerability, but at the time of this writing the backdoor still existed.
How would this work in the real world?:
- The user will get an e-mail asking them to review a document or visit a webpage. This document could be coupons, someone’s CV or contract.
- The user will click on the link and be redirected to Sharepoint which will ask to open the document in Word. If the user accepts, Word will request the document from the malicious webpage.
- The malicious webpage in turn will ask Word for an Office 365 token. The malicious webpage gives Word a legitimate looking document in return. The attacker will then have the Office 365 token and access to the organization’s data.
This is a serious potential threat to organizations and companies that use Office 365. Important company data can be stolen without anyone knowing. The attacker could also monitor the data which could be confidential. The attacker also has access to delete the data.
What Can I Do To Protect My Business?
Until Microsoft comes up with a solid solution to this vulnerability, users should not open any unknown or suspicious looking emails. They should also confirm from known senders to verify the authenticity of the email. It is also important to absolutely avoid clicking on any unknown URLs and links or open attached documents in a file.
For further assistance, let your office IT support know about this vulnerability and stay ahead of a corporate data breach.
Read More