by Ophtek, LLC | Sep 25, 2018 | Cyber Attack, Hacking, malware, Password Security, Phishing, Phishing Email, Ransomware, Security, Security Threats
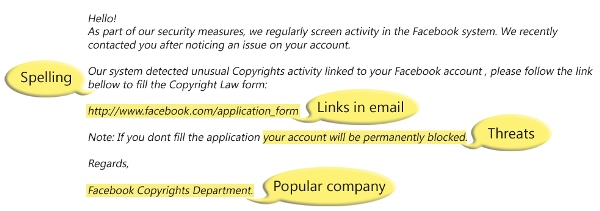
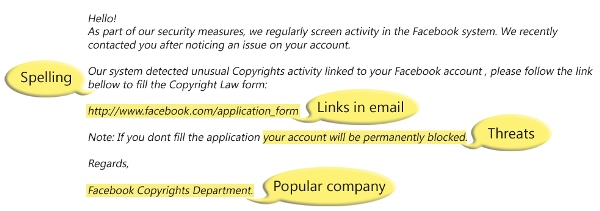
Phishing is big business for hackers and you can rest assured that it’s a niche they’re keen to exploit, but how do you know when you’re being phished? Kaspersky Lab reported around 246 million phishing attempts being executed in 2017, so it’s fairly clear that...
by Ophtek, LLC | Sep 18, 2018 | Cyber Attack, email links, Hacking, malware, Password Security, Phishing, Phishing Email, Security
You may think that political parties understand the need for good security, but back in 2016 the DNC suffered a major hack due to phishing emails. Thanks to a sustained attack, Russian hackers were able to infiltrate email accounts of those involved within Hilary...
by Ophtek, LLC | Sep 11, 2018 | Hacking, malware, Phishing, Phishing Email, Security, Security Threats
Phishing emails are the scourge of our inboxes and there seem to be more and more each week, so what should you do when you receive a phishing email? The aim of phishing emails is for the sender of said emails to obtain sensitive information from the recipient. This...

by Ophtek, LLC | May 21, 2018 | Backup and Recovery, Hacking, Security, Servers, Windows Server
The computer servers that support your business are the backbone that keeps your organization productive, but how do you keep your business servers safe? Every week seems to bring a new security threat and you can rest assured that the number and ferocity of these...
by Ophtek, LLC | Apr 6, 2018 | bitcoin, cryptocurrency, Hacking, Security, Security Threats
Hackers are now infecting websites in order to take control of your PC’s processor and help power the resource heavy activity of cryptocurrency mining. Cryptocurrencies, such as Bitcoin, have been generating countless headlines in the last year due to the huge values...

by Ophtek, LLC | Mar 8, 2018 | Cyber Attack, Hacking, Internet of things, IOT, malware, Password Security, Security, Security Threats
The Internet of Things (IoT) has a new security threat and this time it uses peer-to-peer communication to spread, infect and compromise devices. In January 2018, security researchers working for Bit-defender discovered a new botnet which, although not related, has...