You would like to think that your security software keeps you secure and, on the whole, it will. But there is the chance it could be turned against you.
One of the most trusted anti-malware tools is Microsoft’s Windows Defender app. Originally launched in 2005 – as Microsoft AntiSpyware – Windows Defender is a free tool which offers real-time protection against infected files and websites. It’s a highly effective piece of software and one that all Windows users should ensure is running. But, in an ironic twist, Windows Defender has fallen victim to a vulnerability. And, as you would expect, hackers have been keen to capitalize on it.
The Windows Defender Vulnerability
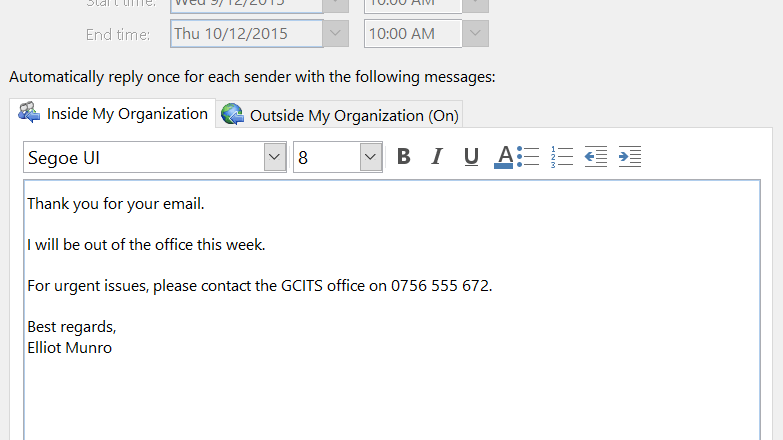
The basic process of Windows Defender is that it scans files and activity on a PC for any malicious potential. If these files are considered suspicious then they will be quarantined by Windows Defender; the user then has the option to either restore or delete the file. However, a problem has been discovered in Windows Defender in the form of CVE-2021-1647. This code, allocated by Microsoft, indicates that it’s a vulnerability in Windows Defender which allows remote access to the app.
By allowing remote access to Windows Defender, this vulnerability grants hackers the chance to turn the app against its user. Instead of scanning malicious files and quarantining them, remote users will program Windows Defender to execute these files. Therefore, a hacker could send infected files to a user safe in the knowledge that Windows Defender will do the hard work for them. It’s a serious threat and one which could cause major problems for your network in a matter of seconds. The exploit has been recorded as active in the digital wild, so this demonstrates that hackers have been aware of it for some time.
Defending Windows Defender
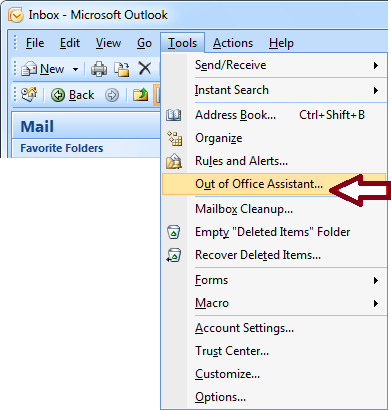
It may sound a tall order to defend a piece of software there to defend you, but this is the world we live in. Thankfully, putting safety measures in place is relatively simple. The vulnerability in question has been fixed thanks to a patch swiftly released by Microsoft. This will be installed automatically and requires no work on the user’s part. Naturally, this does not mean that Windows Defender is 100% secure, the threat of further exploits being discovered remains a possibility. But, by ensuring that automatic updates are in place, your system will be safer than before.
Final Thoughts
Vulnerabilities in PCs are all too common and even Microsoft are not immune from these flaws in their products. The Windows Defender vulnerability – and others such as Zerologon – underline the importance of installing updates. The simplest way to secure your PC is by making sure it has the best chance to defend itself. Accordingly, updates need to be installed as soon as possible. When it comes to Microsoft updates, these can be set to install automatically. This gives you the best chance of staying ahead of exploits and any hackers using them.
For more ways to secure and optimize your business technology, contact your local IT professionals.
Read More