PDF files are vital for business as they allow files to be sent from business to business without room for editing. However, the software is far from safe.
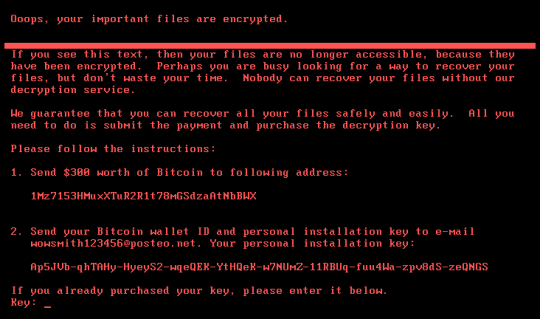
The most popular software for viewing PDF files is Adobe Reader and this has regularly had its security flaws laid bare by hackers such as a font vulnerability in 2015 and a ransomware exploit earlier in 2017. Considering that Adobe are considered the kings of PDF software, it’s no surprise that other builders of PDF software are struggling to cope with security flaws being exploited; a case in point is the Foxit PDF reader.
A popular alternative to Adobe Reader, Foxit PDF saw early success when it was able to gain customers from Adobe due to well publicized security flaws in Adobe Reader. Now, though, hackers clearly have their eyes on Foxit’s huge user base and are keen to discover security flaws in Foxit PDF. Let’s take a look at what’s been happening.
Discovering the Flaws in Foxit
Steven Seeley and Ariele Caltabiano – two security researchers – systematically dismantled the code for Foxit Reader and were able to uncover not one, but two serious security flaws. Capable of tricking Foxit Reader into loading malicious websites, these flaws had the potential for malware to be downloaded and whole systems to be compromised. Once these findings were made public, Foxit claimed that their software had an in-built security procedure – known as ‘Safe Reading Mode’ – to counter this. Whilst this is all well and good, many users had deactivated this procedure due to its oversensitive calibration.
At first, Foxit were resolute in their belief that a patch was not required to prevent any exploit taking place through its software, but the company eventually relented and a patch was released that allowed users to deactivate ‘Safe Reading Mode’ but not at the expense of any vulnerabilities being opened up. However, while this patch was made available, it was the users’ responsibility to ensure that this patch was executed and installed on their systems.
Patches are CRUCIAL!
The Foxit Reader vulnerabilities have highlighted that software can never be 100% safe and, in fact, many of these vulnerabilities may be completely unknown to the vendor – a flaw known as a zero-day vulnerability. Thankfully, most software manufacturers regularly provide updates and patches to help secure and improve their products. Executing and correctly installing these patches though is a manual task that users must make sure they complete as soon as possible.
Patches are usually released as automatic updates that sync with your software, but this can easily be deactivated – mostly because PC users don’t like to be irritated by popups. However, this small irritating task which, let’s face it, only occasionally takes up a tiny fraction of your day, can make a huge difference to the security of your system. Ignore software patches and you run the risk of your entire system being compromised and your organization being forced to down tools.
For more ways to secure and optimize your business technology, contact your local IT professionals.
Read More