Linus Sebastian, owner of popular YouTube channel Linus Tech Tips, has revealed how he woke at 3am in the morning to find his channel hacked.
Linus Tech Tips is a YouTube channel which delivers technology-based content to over 15 million subscribers. Driven by Sebastian’s passion for technology, the channel has been running for 15 years and proven to be wildly successful. So, not surprisingly, it made a tempting target for hackers. As well as Linus Tech Tips, two other channels associated with Sebastian – TechLinked and Techquickie – were also compromised in this attack.
While your organization may not run a YouTube channel, the method in which Linus Tech Tips was hacked could be applied to any IT system. Therefore, it’s crucial that we learn about session hijacking.
What Happened to Linus Tech Tips
Alarm bells started ringing for Sebastian when he was woken at 3am to reports of his channels being hacked. New videos had been loaded and were being streamed as live events. But, far from being productions sanctioned by Sebastian, they were rogue videos featuring crypto scam videos apparently endorsed by Elon Musk.
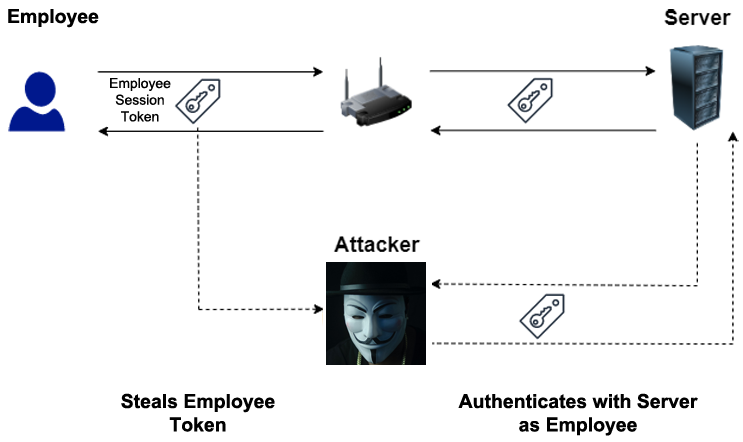
Desperately, Sebastian repeatedly tried to change his passwords, but it made no difference; the videos continued to be streamed. Sebastian was equally puzzled as to why the associated 2FA processes hadn’t been activated. Eventually, he discovered the attack was the result of session hijacking.
A member of Sebastian’s team had downloaded what appeared to be a PDF relating to a sponsorship deal, but the file was laced with malware. Not only did the malware start stealing data, but it also retrieved session tokens. You may not be familiar with session tokens but, effectively, these are the authorization files which keep you logged into websites. So, when you return to that website, you don’t have to re-enter your login credentials each time. Unfortunately, for Sebastian, it gave the threat actors full and unauthorized access to his YouTube channels.
How Do You Prevent Session Hijacking?
Once it had been established that compromised session tokens were behind the breach, YouTube was able to swiftly secure Sebastian’s channels. Nonetheless, the ease with which the threat actors managed to bypass login credentials and 2FA is troubling. This means it’s vital you follow these best practices to protect against session hijacking:
- Understand what malware is: the attack on Linus Tech Tips was the result of malware and social engineering combining to deliver a sucker punch. Accordingly, educating your staff through comprehensive and regular refresher courses should be a priority. This will allow your staff to identify threats before they are activated and protect your IT systems from being compromised.
- Don’t use public WiFi: unsecure networks such as public WiFi found in cafes and airports pose a significant risk to your data, and this includes sessions tokens. Therefore, unless you have access to a VPN, where your data will be encrypted, you should avoid connecting to public WiFi.
- Perform system updates: the malware behind session hijacking will often take advantage of vulnerabilities in software. Consequently, this should act as the perfect motivation to keep your software updated. The simplest way to achieve this is by setting up automatic updates, this will ensure your software’s security is maximized as soon as updates are released.
For more ways to secure and optimize your business technology, contact your local IT professionals.