2018 has been a year where malware, ransomware and data breaches have barely been out of the headlines, but what’s in store for cyber-security in 2019?
As long as there’s a digital landscape, hackers will continue to launch an array of attacks that take in numerous different techniques. And, most importantly, they will continue to evolve their methods to avoid detection and cause more damage to networks and the PCs on them. With this in mind, it’s perhaps the best time to take a look at the security trends which will be most important for your organizations defenses next year.
To help you get prepared for next year, we’re going take a look at some of the major security trends to look out for in 2019.
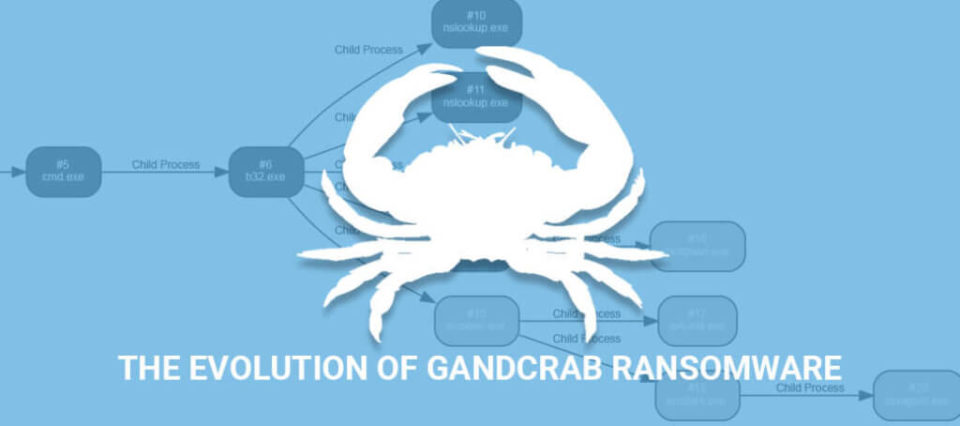
Backups will continue to be Crucial
With ransomware still remaining a prevalent and major threat to secure and essential data, backing up your data regularly and rigorously will be a vital task for all organizations. Backups may seem a costly affair in terms of budget and time, but it only takes one employee to fall victim to a ransomware scam for your entire network’s data to be compromised. And with new ransomware scams such as Zenis deleting backups, it’s essential that offsite and non-network backups are also held.
Coinminer Malware Remains a Threat
Cryptocurrency is still a lucrative business and mining for cryptocurrency continues to generate large amounts of cash. However, whilst this is perfectly legal and above board, the use of coinminer malware is far from legal or ethical. Due to the amount of processing power involved in mining for cryptocurrency, hackers are using malware to enslave PCs remotely and using their processor power to mine for cryptocurrencies. This form of malware has become harder to detect and more sophisticated throughout 2018, so expect it to evolve further in 2019.
The Hacking of IoT Devices will Increase
Close to 27 billion IoT devices will be connected in 2019 – an increase of nearly 3 billion compared to 2018 – so you can bet your bottom dollar that the number of attacks in this arena will increase accordingly. Unfortunately, many owners of IoT devices are still neglecting to change the default password to access these devices and this is giving hackers free rein to take control of them. Not only does the default password debacle remain an issue, but hackers are now designing malware to take advantage of vulnerabilities in IoT devices.
Security Training
Due to the threats already presented, security training will become paramount in 2019. As hackers evolve their methods of attack at a rapid pace, keeping your organization’s staff aware of these threats is one of the best forms of defense you can employ. Awareness training hammers home the basics of good security practices and you’ll find that these can also be used to combat the new threats which will no doubt go head to head with your security defenses.
For more ways to secure and optimize your business technology, contact your local IT professionals.
Read More