2018, just like 2017 before it, was a year packed full of cyber-security threats that our network defenses constantly tried to keep at bay.
However, the sheer number of attacks that were launched throughout 2018 meant that it was inevitable that breaches would take place. Perhaps your organization was one of the lucky ones, perhaps you were just too late to get on board with good security practices and found yourself hacked. Either way, it’s almost certain that you encountered at least one form of hacking during the year. And, hopefully, your organization managed to, at the very least, learn from the situation and improve your defenses.
With 2018 coming to a close, I decided it was a good time to take a look back over the major threats we experienced to see what we could learn and how we can prepare for 2019.
Ransomware
2017 is known by many security insiders as ‘The Year of Ransomware’ as it appeared to be in the headlines constantly. However, in 2018 there was a sharp drop in ransomware activity. By the end of Q2 2018, Malwarebytes reported that ransomware had fallen out of favor with hackers and was now only ranked as the sixth most popular form of malware. It’s suspected that this drop in activity can be put down to a rise in user awareness of ransomware scams and, perhaps most importantly, the fact that organizations rarely paid any ransom fees. The threat of ransomware, of course, still remains albeit much reduced and vigilance remains key to avoid disruption.
Cryptomining
One of the main reasons for ransomware’s fall in popularity during 2018 is down to the increase in popularity of cryptomining malware. Kaspersky revealed that while ransomware infections have dropped by 30%, cryptomining infections rose by 44.5% over the same 12 month period. And this change in fortunes shouldn’t come as a big surprise. All ransomware guarantees is that a ransom demand will be issued, no incoming funds are guaranteed as organizations often refuse to pay due to having backups. With cryptomining, however, once the infection is in place, the hackers can begin to reap small financial benefits fairly soon.
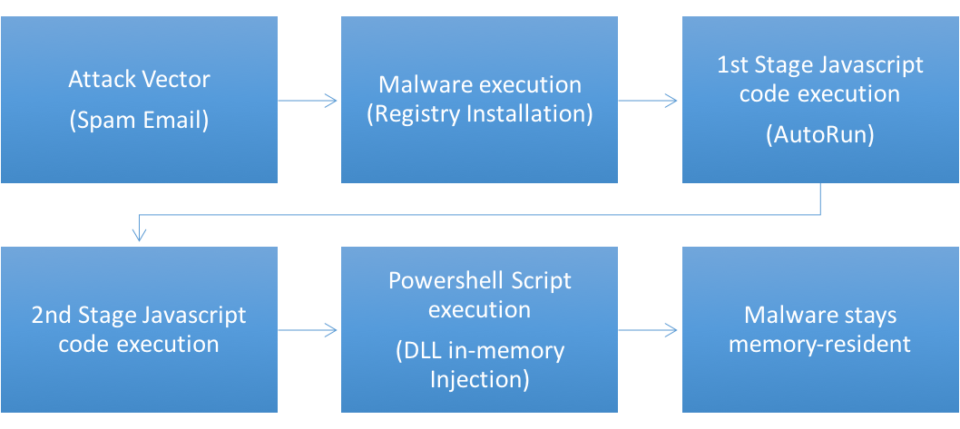
Phishing Emails
Despite the crude appearance and execution of phishing emails, they remain one of the most deceptive threats out there to organizations. Capable of extracting highly sensitive data, phishing emails have continued to enjoy popularity with scammers and hackers. Data from Kaspersky demonstrates that the proportion of spam in email traffic reached 53.49% in September 2018 – up from 47.7% in April 2018. And, through Kaspersky’s defenses alone, just over 137 million attempts to direct users to scam websites were carried out through phishing methods.
Preparing for 2019
There’s never time to rest on your laurels in cyber-security and the data above clearly underlines this fact. While the recent horror stories of ransomware may, to a degree, be muted, this method of hacking has very quickly been replaced with the more discreet techniques of cryptomining. And this is all without mentioning the gargantuan risk posed from phishing emails which remain as popular as ever. Going into 2019, it’s crucial that your organization is aware of the signs, symptoms and ramifications of all the major hacking techniques they may encounter while at work. Only then will you stand your best chance of being protected.
For more ways to secure and optimize your business technology, contact your local IT professionals.
Read More