Some malware is incredibly difficult to remove, but it is removable. However, that very same malware could come back stronger than ever before.
We first reported on the Trickbot malware back in 2017 when it was being used to target banks in the US. Back then it was using web-injection techniques to infect users and steal login credentials. But much can change in three and a half years. Trickbot has steadily evolved to become a much stronger strain of malware. And this, naturally, means that its more dangerous. Therefore, even if you managed to beat Trickbot before, it’s going to require an even stronger battle this time around.
The good news is that we’re going to give you a lowdown on the latest variant of Trickbot and, more importantly, how to beat it.
What is Trickbot?
Trickbot has changed significantly since we last encountered it, so it’s crucial that we take a comprehensive look at it. Since its early days as a banking trojan, Trickbot has evolved several times. Enhancements to its design has allowed it to spread through networks rapidly and with stealth on its side. Trickbot has also been re-engineered to become a malware loader meaning that it can download even more malware to an infected system. It had appeared, last year, that a collection of tech companies had managed to take the Trickbot network down. But it appears that Trickbot is still active.
The latest Trickbot attack uses a social engineering approach to unleash its payload and is targeting legal and insurance companies in the US. Phishing emails are being distributed which inform the recipient that they are responsible for a traffic violation. A link contained within the email promises to deliver proof of this violation. But the true destination of this link is a website which will download an infected ZIP file. This infected file will then connect the user’s PC to a remote server and completes the infection by downloading further malware.
How to Beat Trickbot
Good security practices are essential when it comes to beating malware such as Trickbot. Protect yourself by carrying out the following:
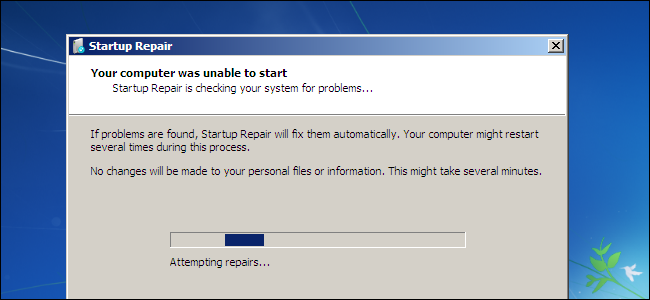
- Install Your Updates: Vulnerabilities in your hardware and software allow malware such as Trickbot easy access into your system. Plug this gap by installing all updates when prompted to and, where possible, set these to automatic installs.
- Teach Email Safety: The busy pressures of the working day mean that we can sometimes switch to automatic when checking our emails. However, by taking a few moments to carry out some basic checks you can make sure you don’t fall victim to malicious emails.
- Two-Factor Authentication: Trickbot is well known for being able to spread through networks like wildfire, but you can limit this spread. By installing a method of two-factor authentication on your network you can make this spread much harder.
- Use Anti-Malware Software: A wide range of anti-malware software is available – much of it at no cost – that can protect your PCs from malware. Windows itself has Windows Defender built into it as standard, so make sure you have something in place. And, don’t forget, make sure the software is turned on.
For more ways to secure and optimize your business technology, contact your local IT professionals.
Read More