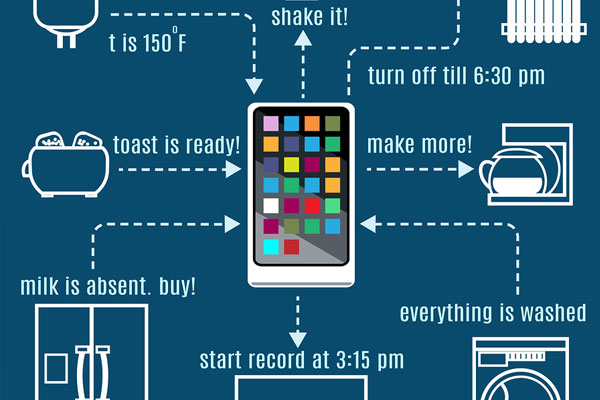
The Internet of Things (IoT) has a new security threat and this time it uses peer-to-peer communication to spread, infect and compromise devices.
In January 2018, security researchers working for Bit-defender discovered a new botnet which, although not related, has similarities to the Reaper botnet. Originally infecting just 12 IoT devices, the Hide ‘N Seek botnet had soon amassed over 32,000 IoT devices by the end of the month. With the ability to steal data, take control of the device and run malicious code, Hide ‘N Seek represents a serious threat.
Understanding new and emerging threats to IoT devices is crucial if you want to protect your organization’s network, so it’s time to investigate Hide ‘N Seek a little closer.
Hide ‘N Seek is No Game
A brand of IP camera manufactured in South Korea appears to be the initial infection source for Hide ‘N Seek, but the botnet is actively attacking other IoT devices. Using randomly generated IP addresses, Hide ‘N Seek attempts to connect to any devices listed against these addresses. If the botnet succeeds in connecting then it either uses default login/password combinations to gain access or performs a brute force attack using a dictionary list to crack the login credentials.
With access obtained, Hide ‘N Seek analyses the device to discover any potential vulnerabilities such as the ability to download malware or launch DDoS attacks. The remote botnet hacker also has the option of executing any command they wish on the infected device; this option provides them with the chance to steal any files they wish. The capabilities of Hide ‘N Seek are clearly advanced and innovative, but what’s even cleverer is that it appears to be constantly redesigning itself to minimize detection.
Communication between the infected devices is made possible by the peer-to-peer network at the heart of Hide ‘N Seek. Using peer-to-peer software for hacking is nothing new, but previous methods have always involved modifying existing torrent software. Hide ‘N Seek is taking hacking to a new level by using completely custom built peer-to-peer software which has no central command unit; therefore, closing this network down is virtually impossible.
Combating Hide ‘N Seek
The advanced design of Hide ‘N Seek is proof that it’s the work of highly skilled hackers, but, once again, the vulnerability being exploited is the use of default passwords. Let’s face it, giving a hacker a key to a locked door is the worst form of security you can imagine, but this is exactly what default passwords are. And this is why password security remains the number one priority for any devices within your network, whether they’re connected to the IoT or otherwise.
By changing these default passwords while devices are on isolated networks, your organization can seriously increase the strength of their defenses. Otherwise, you’re leaving your networks at the mercy of malicious botnets such as Hide ‘N Seek. And, believe me, just as Reaper wasn’t the last IoT botnet, neither will Hide ‘N Seek be the final word in hacking in this new IoT landscape.
For more ways to secure and optimize your business technology, contact your local IT professionals.
Read More