Backdoors are a point of access which can be illegally installed to give hackers free and easy network access; they’re also very difficult to detect.
Unfortunately, for all computer users, backdoor hacks are a form of cyber-attack which is on the rise. And what’s particularly galling for businesses is that they’re becoming harder and harder to combat.
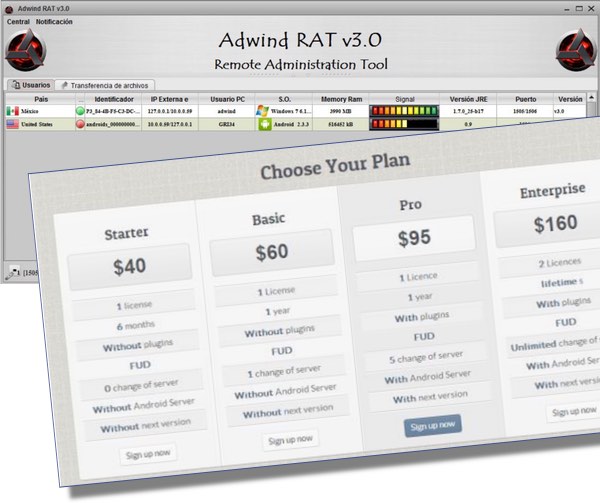
I’ve previously covered variants of backdoor attacks – such as the GlassRAT Trojan – but it’s time I took a closer look at how these backdoors operate.
What is a Backdoor Attack?
Gaining remote access to a computer network is a hacker’s dream, so anything that makes this a possibility will be pursued by hackers; a backdoor to your network is the most straightforward way of achieving this.
It literally is a ‘backdoor’ which hackers can use to come and go as they please without leaving any signs of forcing an entry. And with free rein to access your network, a hacker will seriously compromise the safety of your data and all your systems.
How Do Backdoor Attacks Take Place?

What’s particularly tricky about backdoor attacks is the number of different strategies they employ to breach your defenses:
- Software Exploits – Many pieces of software have backdoors built into them that only the developer is aware of. Sometimes this can be to help aid in maintenance, but there have also been reports of government agencies insisting ‘secret backdoors’ are installed to aid security. However, no matter how secret these backdoors are, there’s always the chance a hacker will discover them.
- Malware – One of the most common methods of establishing a backdoor is through malware which first breaches the network before downloading code to setup a backdoor. As we’ve learned previously, malware can come in many forms such as email attachments and phishing.
Both these methods are troubling as they can take the form of a zero day exploit, so firewalls and anti-malware software are oblivious to these new security threats which leads to a period where the attack simply isn’t detected.
Secondly, the backdoor establishes the hacker with seemingly legitimate credentials and this fails to create any suspicion around the connections being made into your network, so they’re not easy to pick up and gives the hacker plenty of time to run riot.
How to Defend Against Backdoors
Although backdoors are tricky attacks that are difficult to counter, you can still protect your network by taking the following measures:
- Use Smart Monitoring – A whole industry is springing up around cloud based network security which regularly maps what’s happening online in terms of attack activity. By using this data to predict incoming attacks, the software can pre-prepare your system for the assault such as identifying incoming, malicious traffic.
- Don’t Forget The Old Methods – Firewalls and anti-malware software still have a place and can detect a high proportion of backdoor activity e.g unauthorized incoming traffic. Therefore, it’s not quite time to dispose of these quite yet otherwise you run the risk of a simple and quick hack taking place.
For more ways to secure and optimize your business technology, contact your local IT professionals.
Read More