The impact of the Covid-19 can still be felt, with high numbers of employees continuing to work remotely. But how does this affect your cybersecurity?
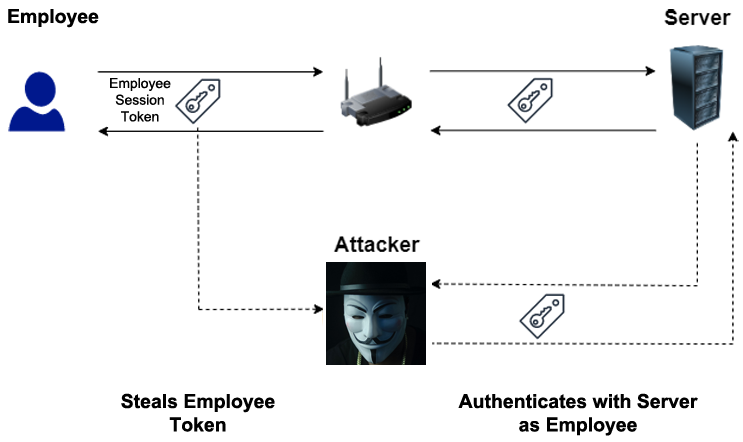
The shift towards remote work was essential at the start of the pandemic, and it has now become a permanent aspect of many employees’ lives. However, while it represents a flexible approach to work, which helps achieve a healthy work/life balance, it also comes with challenges in terms of cybersecurity. With employees working from different locations and connecting to your IT infrastructure from different networks, it’s a complex scenario to manage.
Staying Secure in the Remote Work Era
It’s important your organization takes the necessary steps to strengthen their defenses when it comes to remote working practices. Many of these are simple and can be implemented easily. Therefore, you need to make sure you follow these best practices:
- Avoid Public Wi-Fi: remote working allows your employees to work from anywhere, but this can open them and your servers up to significant risk. In particular, the risk of public Wi-Fi networks – such as those found in coffee shops and public places – should never be underestimated. With little protection in place, these Wi-Fi networks can easily be compromised and risk your organization’s data being harvested. Therefore, your remote employees should be discouraged from using these, instead using secure networks at home.
- Use Multi-Factor Authentication: For remote workers, extra layers of security are everything when it comes to protecting your networks. And this is why multifactor authentication can be a real game-changer in terms of your security. Furthermore, biometric authentication such as Windows Hello allows your business to enhance its security and prevent unauthorized access.
- Use Secure Collaboration Tools: You have to think a little differently when working with remote employees, especially when it comes to collaborating. It’s not as simple as having your entire team in the same room, so collaboration software is crucial. However, this needs to be secure. So, make sure you use secure collaboration tools such as Microsoft Teams, Slack, and Basecamp to ensure your communications remain encrypted and safe
- Monitor Remote Devices: With your remote employees’ devices out of sight, they need to be monitored closely. Endpoint monitoring software allows you to track devices in real time and identify any unusual behaviors. Automatic alerts and notifications can be put in place to ensure you’re aware of any breaches immediately and allows you to take action to neutralize any threats.
- Device Inventory: As many of your IT devices will now be located off-site, it’s vital you keep a device inventory to manage all of them. This allows you to know exactly what devices are accounted for within your business and where they’re currently located. By keeping a device inventory, you minimize the risk of, for example, laptops not receiving updates and becoming vulnerable to threat actors.
- Employee Training: As ever, the most important aspect of cybersecurity for businesses involves employee training. Accordingly, your remote employees need specific training to make sure they understand the risks of remote work. Strong and unique passwords, for example, have never been more important, and being able to identify phishing attempts is equally crucial when an employee is unable to call on the immediate support of their colleagues.
For more ways to secure and optimize your business technology, contact your local IT professionals.
Read More