SMS is one of the most popular ways to confirm two-factor authorization. Accordingly, it’s been adopted by countless organizations. But is it secure?
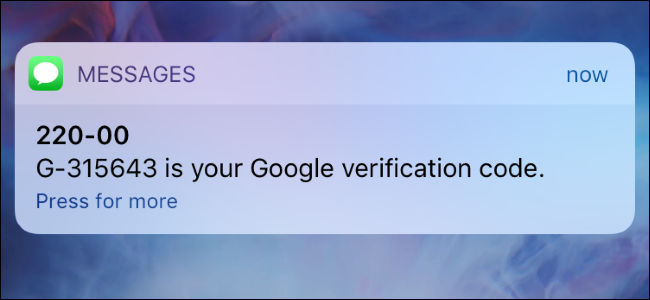
Two-factor authorization is one of the simplest ways to maximize security. Instead of, for example, simply entering a username and password, two-factor authorization requires a little more. So, once the correct login details have been processed, a further level of confirmation is requested. One of the most popular ways to achieve this is through SMS. Users are sent a unique code which must then be entered into the system they wish to access. It’s one of the surest ways to confirm a genuine login.
However, the discovery of a vulnerability in SIM security has left security experts questioning the safety of SMS authentication.
The Problems with SIM Cards
The ease and simplicity of SMS authentication has made it a popular choice with IT experts and PC users. But a study by Princeton University has shone new light on the dangers of SMS authentication. It’s all down to a form of hacking known as a SIM-swap attack. A strain of social engineering, SIM-swap attacks involve deceiving phone carriers into swapping existing phone numbers over to new SIM cards.
With a new SIM card in their possession, the perpetrator is in the perfect position to hijack accounts and sail through two-factor authorization with ease. One of the most worrying aspects of the study was that some major phone carriers were involved. AT&T, Verizon, US Mobile, Tracfone and T-Mobile all failed to prevent SIM-swap attacks taking place. But how did this happen?
After a year-long study, the Princeton researchers were able to determine that deceiving a call center operator was relatively simple. To activate the SIM-swap process, all the researchers had to do was pass a single security challenge. Perversely, to reach this stage, the researchers had to deliberately submit an incorrect PIN. Once asked to confirm personal information, the researchers would plead ignorance to these requests. The next step, by the phone carriers, would be to request details about the last two calls made by that number.
You may think that his information is difficult to obtain, but it’s a lot easier than you would imagine. Social engineering can be used to trick victims into making phone calls quite easily, particularly when financial matters are mentioned. And it was with this information that the researchers were able to initiate the SIM-swap process.
How Can You Secure Two-Factor Authorization?
The results of the Princeton study are worrying and highlight a lack of security on the part of phone carriers. T-Mobile has since confirmed that they have eliminated call logs from their authorization process. But the fact remains that SIM cards have been highlighted as a weak link. And it’s recommended that your organization drops SMS authorization. The preferred method of two-factor authorization is with an authentication app. These apps generate unique two-factor codes on a phone, but remain inaccessible by the SIM card.
For more ways to secure and optimize your business technology, contact your local IT professionals.
Read More