Whether at home or in the office, the low cost and huge benefit of running a gigabit network is too good to pass up. Here’s what you need to know.
What is a Gigabit Network?
Let’s start with what a network, let alone gigabit network means in the context of your office or home. The network is how all of your computers, wifi/wired printers, tablets and even TVs talk to each other.
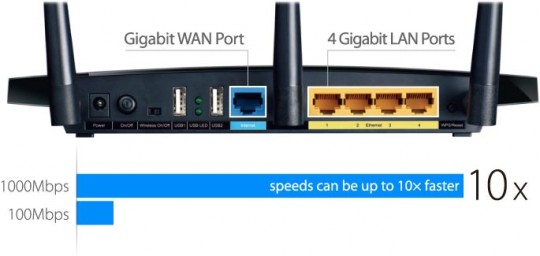
The speed at which your devices talk to each other is determined by your network equipment such as your wireless router and network cables connecting all of your devices to the router. Having equipment and cabling capable of gigabit speeds means you are running 10 times faster than traditional networking equipment often running at 10 or 100mbit speeds.
Benefits of a Gigabit network
- Google fiber could be coming to you
That’s right, gigabit internet could well be accessible to you, helping your network perform better, along with improved traffic flow to better avoid bottle necks.
- Faster file transfer rates and program load times
Up to ten times the speed to help increase communications between your office computers for file sharing, and loading programs over the network. It can also, for instance, considerably reduce the waiting time for backups to complete, compared to the average standard Ethernet rate of 12.5 Mbps.
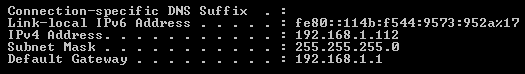
- Your equipment may already be compatible
If your equipment is fairly new, the chances are that it may support running on a Gigabit connection. Equipment such as desktops, LAN switches, cables, and so forth, all need to be able to run 1000 Mbps and have ports that support this too. Category 5e or 6 cables are the best to use in a Gigabit network.
- Old switches/ routers can still work on a Gigabit network
What’s good is that you don’t need to throw your existing switch/router away. You can obtain a standalone gigabit-enabled switch, like a Netgear that can cost around $40, and connect it up your old switch or router.For the low price of setting up a Gigabit network it’s definitely worth the upgrade. Anything that streamlines access to applications, facilitates smooth daily backup operations, or allows access to any shared resource in the company is going to benefit everyone.
For more advice on setting up a gigabit network in your office or home, contact your local IT professionals.
Read More