A single typed character led Windows users straight into a malware trap, showing just how quickly something small can turn dangerous.
Recently, some Windows users running unofficial activation scripts began seeing something strange on their PCs. Rather than a fully usable version of Windows, they were presented with a warning. The scripts – coded by a group called MAS (Microsoft Activation Scripts) – are far from legal, and certainly aren’t supported by Microsoft. As a result of using these scripts, some users were warned that their PCs had become infected with the Cosmali Loader malware.
As ever, deception was at the heart of this attack, and it all came down to a particularly sneaky tweak to a web address.
How One Typo Led to Serious Trouble
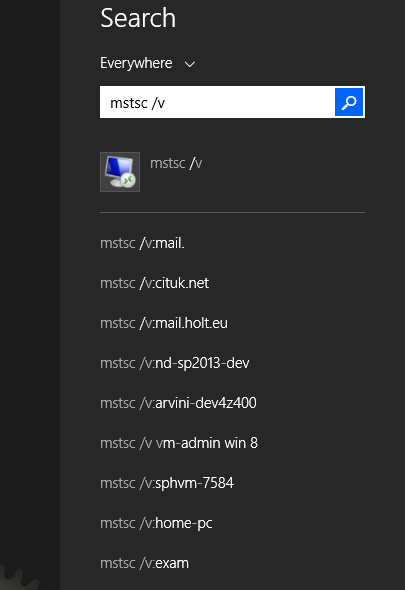
Most of the affected users were attempting to run PowerShell commands on their PC. These commands are typed instructions that can make significant changes to Windows. So, for example, a set of PowerShell commands could easily download code from the internet and then run it on a PC.
The threat actors behind this campaign set up a website with an address that closely mimicked the MAS activation site. This allowed them to place their scripts in front of unsuspecting users. However, the malicious duplicate dropped a single “d” from the address. Users who misspelled the legitimate address could, therefore, easily land on the malicious site without realizing it.
Once on this fake site, the malicious PowerShell command would download and run the Cosmali Loader on the user’s PC. While Cosmali Loader won’t disable your PC or encrypt your data, it’s still a nasty strain of malware. Its modus operandi is to install software which mines cryptocurrency using your computer’s resources and even hands over full control of the infected PC to the hackers.
With the MAS domain – which is, in itself, legally dubious – proving so popular to PC users trying to save a few dollars on software, it’s positioned itself as an attractive proposition for attackers. Therefore, while attacks such as this are rare, they remain an innovative attack method for hackers.
The Dangers of Third-Party Websites
If a single mistyped address can deliver malware, it highlights the issues surrounding trust on the internet and how a sense of constant vigilance is crucial. To avoid getting caught up in similar scenarios, Ophtek recommends these three quick tips:
- Always Use Legitimate Software: Avoid using unofficial activation tools at all times. While these may seem tempting financially, you never know for certain exactly what’s bundled within these tools.
- Double-check URLs: Malicious sites are a major problem online, so it pays to take a few moments to verify that the one you’ve typed into your browser (or the link you’re about to click) is correct.
- Leave PowerShell Commands to the Professionals: If you’re not fully confident with using PowerShell commands, seek advice from someone who is before activating one on your PC. An IT professional will be able to spot any suspicious signs immediately and advise if a PowerShell command is safe or not.
For more ways to secure and optimize your business technology, contact your local IT professionals.