Microsoft has claimed that their latest upgrade to Windows 10 (10S) is immune to all known ransomware. However, it appears that this isn’t quite true.
Windows 10S is a streamlined upgrade of Microsoft’s current operating system (OS) and it promises increased speed, stability and security. Naturally, this claim of invulnerability is certainly impressive, but, effectively, it’s also issued a challenge to the online community to test the strength of this security.
It’s a brave move, perhaps one which was necessary after the various security issues with Windows 10 shortly after its launch, but it’s now looking rather embarrassing for Microsoft as Windows 10S has already been breached.
Hacking Windows 10S

Launched at the start of May, Windows 10S survived several weeks without having its defenses breached, but this security has now come tumbling down. Security expert Matthew Hickey of Hacker House managed to make his way through the security capabilities of Windows 10S in just three hours.
How did he do this though? Microsoft, after all, should know a thing or two about security, right? Well, Hickey actually employed an old fashioned technique of hacking called DLL injection. A particularly sneaky form of hacking, DLL injection runs malware within a running process that is deemed not capable of carrying a threat by the operating system in question.
This hack was carried out by one of the most common malware attacks seen in contemporary hacking, a Microsoft Word document packed full of malicious macros (automated commands). Although Microsoft Word now has an anti-malware system, this does not detect issues with files that have been shared on the network – which is exactly where Hickey had downloaded the infected document to.
Hickey was then able to activate the malicious payload in the Word document and found he was able to take control of the PC by giving himself full administration privileges. Using Metasploit – software designed to look for loopholes in cyber defenses – Hickey eventually managed to secure himself full system privileges. And this meant, in theory, that he could begin disabling firewalls and anti-malware software.
With the system’s defenses completely disabled, Hickey could easily have installed ransomware on the PC, but he refrained from doing this in order to protect other PCs on the network.
An Unhackable OS?
At no point did Microsoft claim that Windows 10S was 100% protected from any form of hacking, but by claiming that it was safe from ransomware they were setting themselves up for a mighty fall. And now that Matthew Hickey has revealed just how easy the hack was – and a three hour hack is relatively quick in terms of a previously unhacked operating system – it’s likely that even more exploits will be revealed.
And, although Hickey’s attack was a ‘friendly’ hack, it underlines just how fragile cyber security can be. Despite all the bold claims by Microsoft, Windows 10S doesn’t appear to be any more secure than previous versions and this is very troubling for consumers.
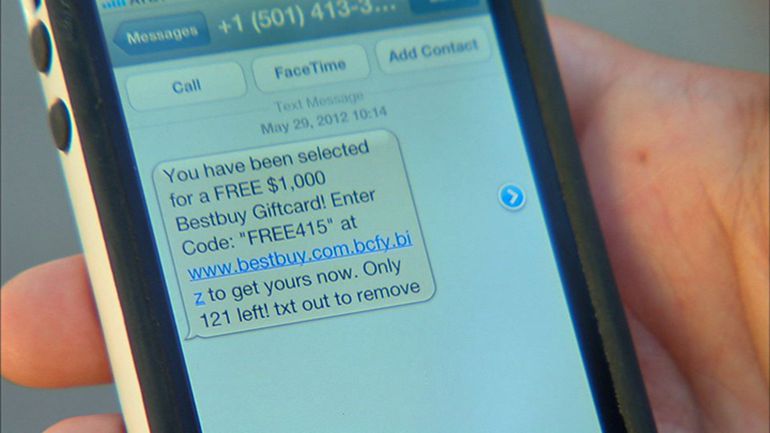
Once again, user knowledge and awareness is highly important as the root cause of this attack was an infected Word document. Your employees must understand the important of identifying malware and not rely on software as, even when Microsoft are involved, it’s impossible to claim something is secure enough to give you full protection.
For more ways to secure and optimize your business technology, contact your local IT professionals.
Read More