by Ophtek, LLC | Oct 24, 2015 | Security
It’s essential for businesses to protect their data assets from any potential security threat. Here are tips to help your business achieve this. The world of IT security, however, can be an intimidating landscape and many business owners struggle to put a plan of...
by Ophtek, LLC | Oct 22, 2015 | Security
Users running Apple’s iOS software may have been exposed to a nasty piece of malware which threatens to steal user data and make unauthorized app purchases. This malicious software has been dubbed ‘KeyRaider’ and has been responsible for uploading sensitive user...

by Ophtek, LLC | Oct 20, 2015 | Security
It’s not just PCs that are at threat of malicious software (malware), smartphones are fast becoming the prime target for malware, but how has this happened? First of all, what exactly is malware? Essentially, it’s a nasty string of code or a program which enters...
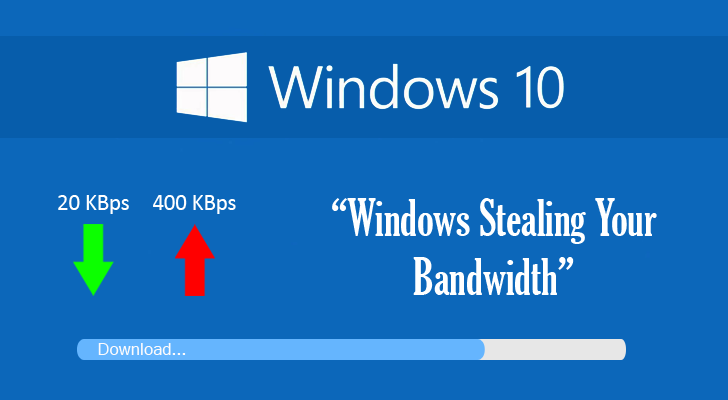
by Ophtek, LLC | Sep 21, 2015 | Network
Microsoft’s Windows 10 claims to improve the PC experience, but the forced update is causing data caps to blow and creating financial chaos for its users. No one likes to receive a huge bill for their wireless costs, so many consumers are furious that this is...
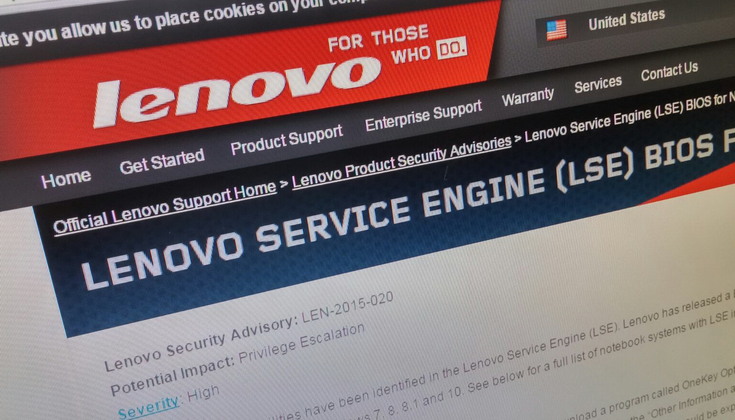
by Ophtek, LLC | Sep 18, 2015 | Security
It’s irritating to find a fresh PC full of unnecessary preloaded software, but a Lenovo rootkit has been found sneaking software onto PCs after installation. Preloaded software such as this is called ‘bloatware’ as it uses up vital system resources, but provides...