Google’s Chrome is the most widely used browser on the internet, but this dominance also makes it a major target for hackers.
The popularity of Chrome means that it’s a vital asset for PC users and this applies to both domestic and business settings. One of the major advantages of Chrome is that it’s supported by a vast database of add-ons. These add-ons, which are coded by official developers or third-party coders, can be installed within seconds and provide an enhanced browsing experience. But the ease with which these add-ons can be released makes them a security risk.
This risk has been brought into sharp focus by a security lapse which has led to 32 million downloads of malicious spyware. And this startling figure is why we’re going to take a closer look at the situation.
What is a Chrome Add-on?
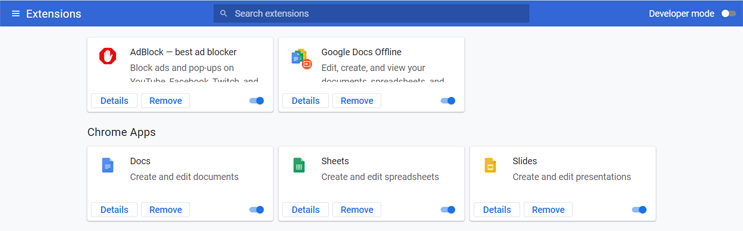
You may be wondering what a Chrome add-on is and it’s a good question which we will quickly cover. Add-ons, also known as extensions, allow users to modify Chrome in a way which adds extra features and accessibility e.g. Save to Google Drive. The add-ons are built using web technologies such as JavaScript and are embedded into the user’s browser where they can be turned on and off.
How Has Spyware Infiltrated Chrome Add-ons?
Security researchers have discovered that a number of Chrome add-ons have not been delivering the benefits they promise. These particular extensions, available for free, advertise themselves as providing services which include converting files to different formats and warning about malicious websites. However, these add-ons contain a nasty surprise in the form of spyware. And this spyware has been used to record browsing data and login credentials. Around 70 suspicious add-ons, all uploaded with fake contact details, have been identified and since removed by Google.
How Can You Protect Yourself Against Malicious Add-ons?
The busy digital age we live in means it’s easy to lose focus with what’s happening on our screens. But vigilance is crucial when it comes to threats such as malicious add-ons. Therefore, it’s important that you practice the following when working with extensions:
- Check Permissions: Whenever you install an add-on it will detail the permissions that it requires to run. These could range from asking for permission to access your hard drive through to analyzing your browsing data. An add-on which asks for a large number of permissions should immediately ring alarm bells. Most important, however, is the nature of these permissions. Anything which feels too invasive should be declined and an alternative sought.
- Audit Your Add-ons: It’s always a good idea to monitor the add-ons you have installed in your browser. Any that you deem as no longer necessary should be removed; auditing your add-ons should be carried out every month. This will ensure that your browser does not become bloated with add-ons and minimizes the risk of rogue extensions being present.
- Ask a Professional: If in doubt, always reach out to an IT professional before installing an add-on. Their experience of identifying malicious software will allow them to quickly determine whether it is safe or not. And, don’t forget, only ever consider an add-on which provides an invaluable benefit. Otherwise it is recommended to continue without it.
For more ways to secure and optimize your business technology, contact your local IT professionals.