 Hackers are now turning to employees of organizations to help breach their defenses and this can be knowingly or unknowingly, but how are they doing it?
Hackers are now turning to employees of organizations to help breach their defenses and this can be knowingly or unknowingly, but how are they doing it?
As this hacking technique doesn’t rely purely on digital attacks, it’s a unique problem in the world of cyber-security. Sure, the end result is the same in that the hackers want to access digital information, but this method of getting a head start makes their attacks more covert than ever.
To help you understand how these exploits can be initiated and unfold, I’m going to show you 4 ways that hackers are hacking your employees.
- USB Stick Hacks
USB sticks can cause huge issues for your PCs due to the amount of automated hacking software which can easily be loaded onto them; in some extreme cases, USB sticks can also be used to completely destroy a PC. More often than not, these attacks can be initiated by old fashioned human curiosity. A recent study showed that of 297 flash drives left in a college parking lot, over half of these drives ended up being plugged into a PC. Therefore, staff need to be made aware that unauthorized devices should never be plugged into their workstations.
- Website Information
Many organizations display details of their employees on their website in order to show the people behind the business. Whilst this is a great method for engaging customers and clients, it also allows hackers to begin building a portfolio of information on targeted individuals e.g. with access to photos and email addresses, it’s possible to not only target these email addresses, but actually track them down in real life. This opens up your employees to direct approaches and is a good reason why information about employees should be minimized on the public internet.
- Phishing
The oldest, and perhaps simplest, method of hacking employees is by phishing. Deceptively convincing, phishing attacks often take the form of genuine looking emails requesting personal information. The most common technique is for the hacker to fake a company email in order to obtain sensitive data e.g. emails are often dispatched which appear to originate from the organization’s IT department and request login details, but actually originate from outside the business. Employees need to receive regular training on how to spot phishing emails.
- Vishing and Smishing
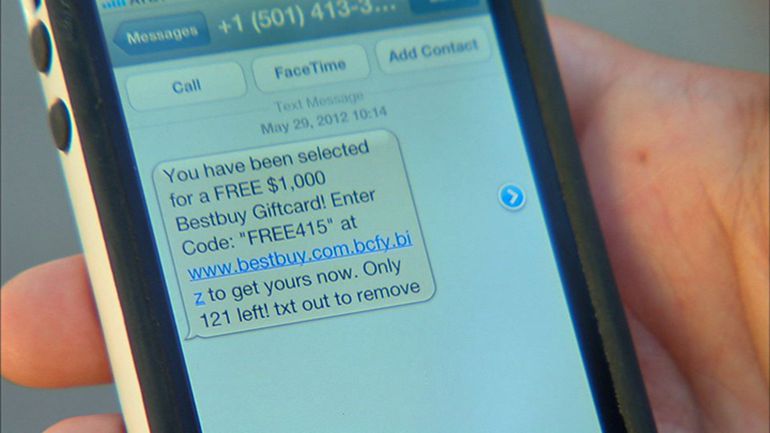
A relatively new approach to hacking employees is via vishing (obtaining information via phone calls) and smishing (mining for data through SMS messaging). Vishing often takes the form of a phonecall from a potential customer, but it’s actually a hacker trying to learn information about the organization’s structure and security through careful questioning. Smishing tends to target employees with links that they’re encouraged to click and then forwards them to a phishing website to extract data. Again, good training is crucial to ensure your staff can recognize these threats.
These four methods of hacking your employees use a number of highly sophisticated methods that prey on human curiosity and misplaced trust. They’re also remarkably easy to execute, so the key is to remember that regular training to increase awareness is the best defense against such attacks.
For more ways to secure and optimize your business technology, contact your local IT professionals.






